Sponsored by Netskope
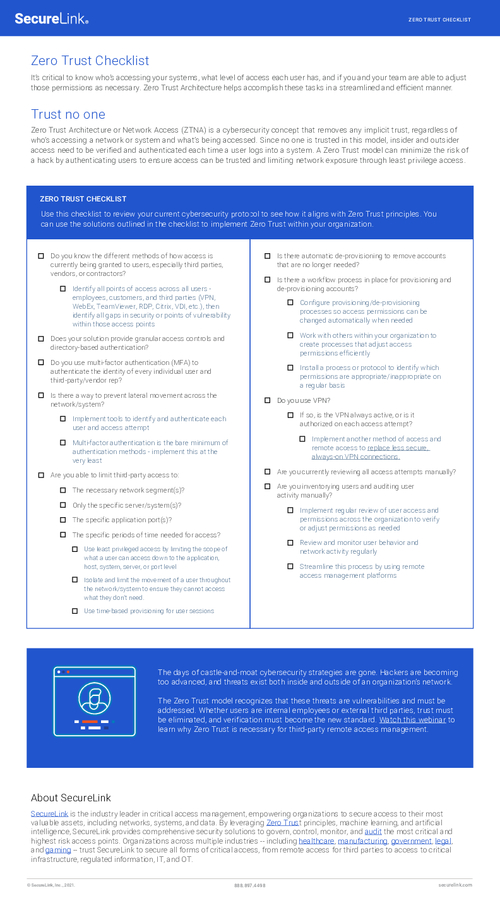
Sponsored by SecureLink
Checklist: Is Zero Trust In Your Cybersecurity Strategy?
Sponsored by Cribl
Top Six Techniques to Control Your Log Volume
Sponsored by Cyberark
Take Remote Access Enablement to the Next Level
Sponsored by Duo Security
Protecting Against Ransomware: Zero Trust Security for a Modern Workforce
Sponsored by Duo Security
The Essential Guide to Securing Remote Access
Sponsored by Menlo Security
Isolation Solves the Cybersecurity Dilemma
Sponsored by Menlo Security
A Winning Remote Work Game Plan
Sponsored by Menlo Security
Stop Malware for Good: A New Game Plan for Securing Federal Agencies
Sponsored by Menlo Security
Reimagining Online Security for Federal Agencies
Sponsored by Menlo Security
Ransomware: State & Local Governments Fight Back
Sponsored by Palo Alto Networks
Secure Access Service Edge for Manufacturing
Sponsored by Palo Alto Networks
Secure Remote Access for Financial Services at Scale
Sponsored by Palo Alto
Fortune 100 Financial Services Company Reduces Attack Surface with Cortex Xpanse
Sponsored by Palo Alto Networks