Sponsored by CA Technologies
Sponsored by Wombat
What's Wrong With Traditional End-User Anti-Phishing Training?
Sponsored by ReversingLabs
The Need For a More Comprehensive Malware Analysis Platform
Sponsored by Certified Security Solutions (CSS)
IoT Security for the Future: 5 Guiding Tenets
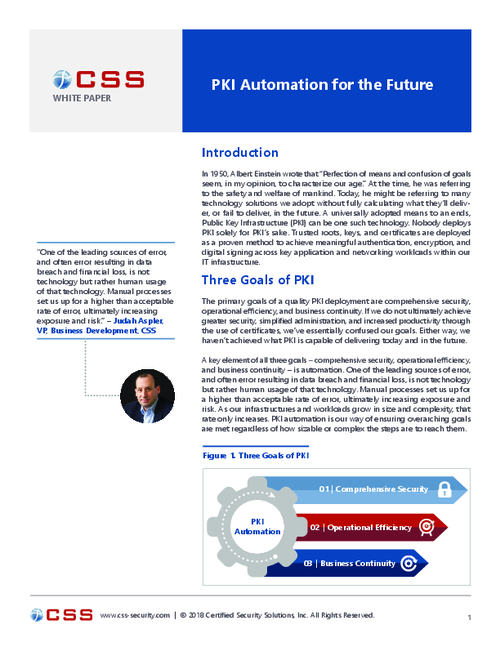
Sponsored by Certified Security Solutions (CSS)
Comprehensive Security, Operational Efficiency, and Business Continuity
Sponsored by Certified Security Solutions (CSS)
Providing Strongly Authenticated Device Identity During the Era of IoT
Sponsored by Digital Guardian
6 InfoSec Pros on the Top Healthcare Security Considerations
Sponsored by ReversingLabs
How to Analyze Malware Without Exposing Sensitive Data
Sponsored by Ping Identity
Digital Identity Solutions for Financial Services
Sponsored by Ping Identity
Improve and Secure Healthcare Delivery with Identity Management
Sponsored by iboss
Leveraging SaaS to Fill the Skills Gap
Sponsored by Entrust Datacard
Forrester Report: Modern Authentication Methods To Protect Your Business
Sponsored by iboss
SaaS: The Solution For Closing The Skills Gap
Sponsored by McAfee
Demystifying Fileless Threats
Sponsored by McAfee