Sponsored by Cyberark
Identity Security: Why it Matters and Why Now
Sponsored by Cyberark
Identity Security for Dummies
Sponsored by Cyberark
The CISO View: Protecting Privileged Access in a Zero Trust Model
Sponsored by Cyberark
Blueprint for Identity Security Success
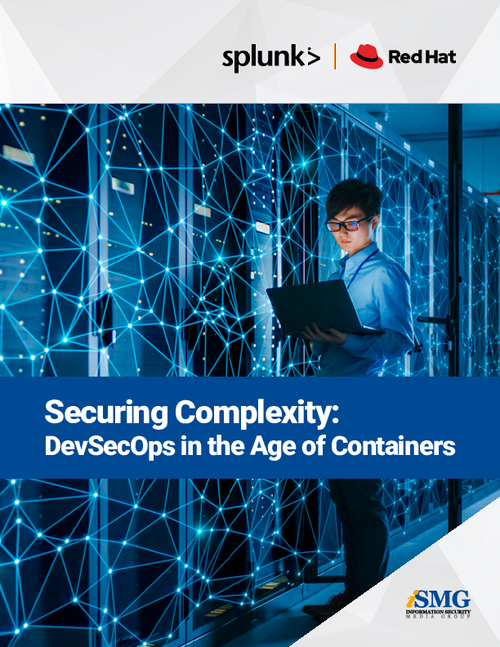
Sponsored by Splunk
Securing Complexity: DevSecOps in the Multi-Cloud Environment
Sponsored by Red Hat
6 Ways to Promote IT Automation Adoption Across your Organization
Sponsored by Red Hat
5 Benefits of IT Automation for the Public Sector
Sponsored by Red Hat
5 Ways to Implement Successful DevSecOps using IT Automation
Sponsored by Red Hat
Guideline for securing Red Hat Ansible Automation Platform
Sponsored by VMWare
US Security Insights Report - GSI Report
Sponsored by Abnormal Security
CISO Guide to Vendor Email Compromise (VEC) - The Risk of VEC and How to Stop It
Sponsored by Pondurance