Sponsored by Claroty & Rockwell Automation
Sponsored by Corsha
Halt and Secure: Protecting OT to IT in the Cyber Frontier
Sponsored by Rockwell Automation
Anatomy of 100+ Cybersecurity Incidents in Industrial Operations
Sponsored by Rockwell Automation
Anatomy of Industrial Cyberattacks Infographic
Sponsored by Rockwell Automation
OT/ICS Incidents: Rising Risks and Regulations Demand Proactive Protection
Sponsored by Corsha
From Legacy to Leading Edge: Challenges & Solutions in OT to IT Security
Sponsored by Palo Alto Networks
Gartner Insights into Operational Technology Security
Sponsored by Palo Alto Networks
Economic Benefits of Industrial OT Security
Sponsored by Palo Alto Networks
Securing all OT Operations with Zero Trust Security
Sponsored by HID Global
The Mobile Marvel: A Swipe at Safety and a Pinch of Convenience
Sponsored by HID Global
Unlocking Possibilities: Safeguarding Cyber Networks
Sponsored by HID Global
When One Door Opens: An Apple Wallet Badge Unlocks Many
Sponsored by Dragos
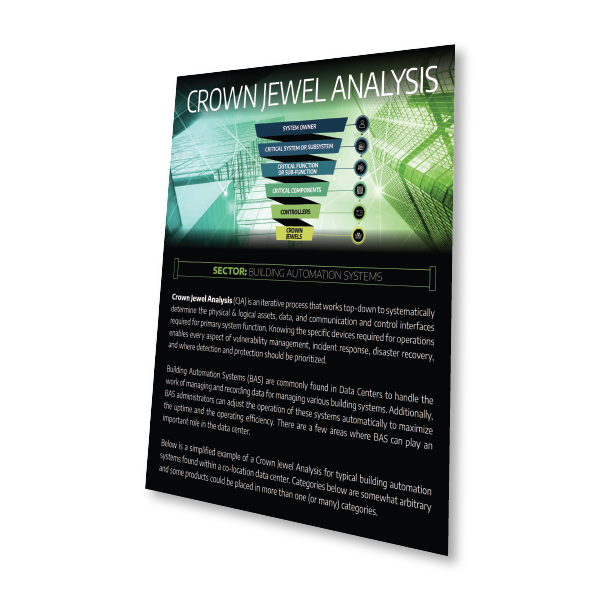
Infographic | Crown Jewel Analysis for Building Automation Systems
Sponsored by Cyolo
The State of Industrial Secure Remote Access
Sponsored by Cyolo