Sponsored by FireMon
Sponsored by Firemon
Data-driven Security Meets the 21st Century
Sponsored by Forcepoint
9 Steps to Building an Insider Threat Defense Program
Sponsored by Forcepoint
From C&A to A&A: The RMF Shoe Has Dropped
Sponsored by Forcepoint
Federal Agencies Make the Case for Modern Network Security Operations
Sponsored by Level 3
Is Your Organization Prepared for Today's Sophisticated Cyber Threats?
Sponsored by Level 3
2017 Cyber Threat Checklist: Are You Prepared?
Sponsored by PhishMe
Why Can't We Solve Phishing?
Sponsored by Carbon Black
Streaming Prevention: Breakthrough Prevention That Stops All Forms of Attacks
Sponsored by Carbon Black
Ransomware on the Rise: An Enterprise Guide to Preventing Ransomware Attacks
Sponsored by Carbon Black
Out with the Old, In with the New: Next Generation Antivirus
Sponsored by Carbon Black
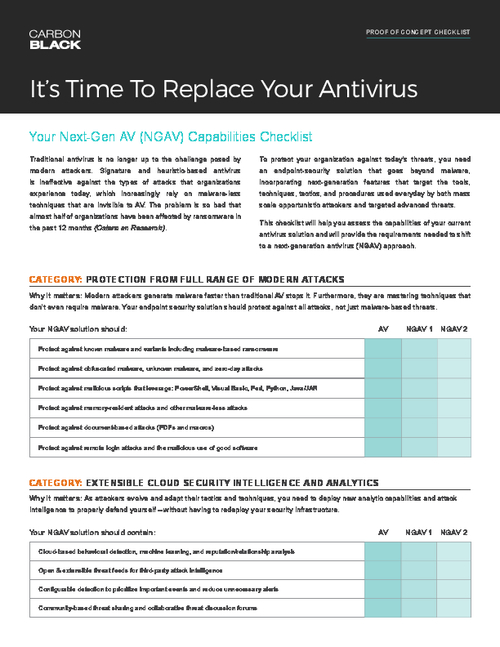
Replace Your Antivirus (AV) Checklist: It's Time to Replace Your Antivirus
Sponsored by Carbon Black
Motivated Attackers Are Not Slowing Down: Trends and Predictions for 2017
Sponsored by Carbon Black
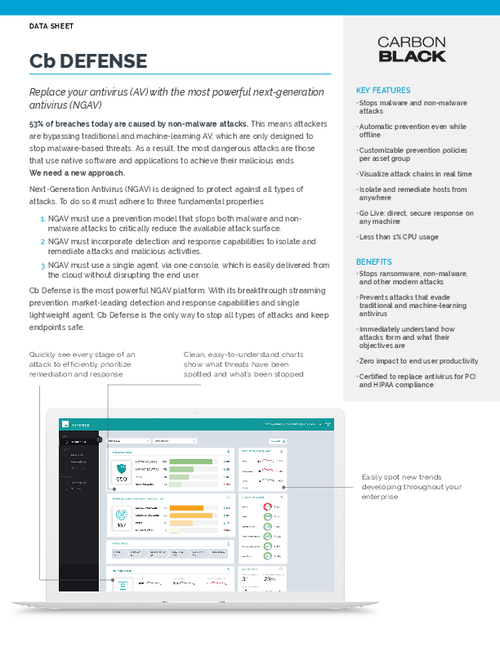
Critically Reduce the Available Attack Surface with Next-Gen Antivirus
Sponsored by Veriato