Sponsored by HelpSystems
Sponsored by BlackBerry
Ready or Not? GDPR Maturity Across Vertical Industries
Sponsored by BlackBerry
What Challenges will IoT Bring to Your Enterprise?
Sponsored by Group-IB
Preventing and Investigating Cybercrime
Sponsored by BitSight
Common Security Vulnerabilities in Organizations
Sponsored by BMC Software
A Closer Look at the SecOps Challenge
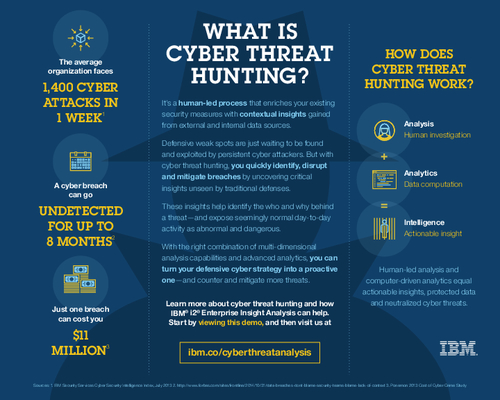
Sponsored by IBM
Counter and Mitigate More Attacks with Cyber Threat Hunting
Sponsored by Digital Guardian
After Wannacry: Getting Ahead of Ransomware
Sponsored by VMware and Intel
Network Automation Makes your Life Easier
Sponsored by ServiceNow
Improve Incident Response Efficacy, Efficiency and Productivity
Sponsored by Rsam
A Modern Security Assessment Model that Breaks from Tradition
Sponsored by Rsam
Assess, Manage and Respond to Security Risks in Heathcare
Sponsored by IBM
What is Cyber Threat Hunting?
Sponsored by IBM
How PSD2 Will Affect Payment Service Providers
Sponsored by IBM