Sponsored by Expel
Sponsored by ServiceNow
Forrester TEI ServiceNow Security Operations Solutions
Sponsored by Open Raven
Finding & Eliminating Sensitive Data in Logs
Sponsored by Team Cymru
What Elite Threat Hunters See That Others Miss
Sponsored by Team Cymru
Forrester Total Economic Impact Whitepaper
Sponsored by Team Cymru
Case Study: Leading Financial Institutions
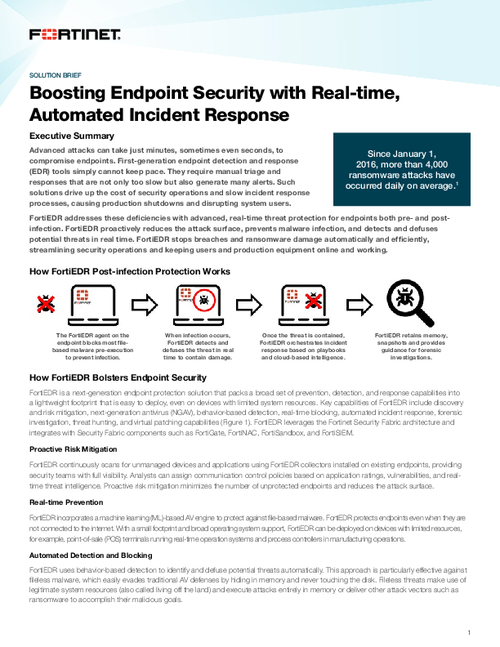
Sponsored by Fortinet
Boosting Endpoint Security with Real-time, Automated Incident Response
Sponsored by Fortinet
Hidden Costs of Endpoint Security
Sponsored by Fortinet
6 Obstacles to Effective Endpoint Security
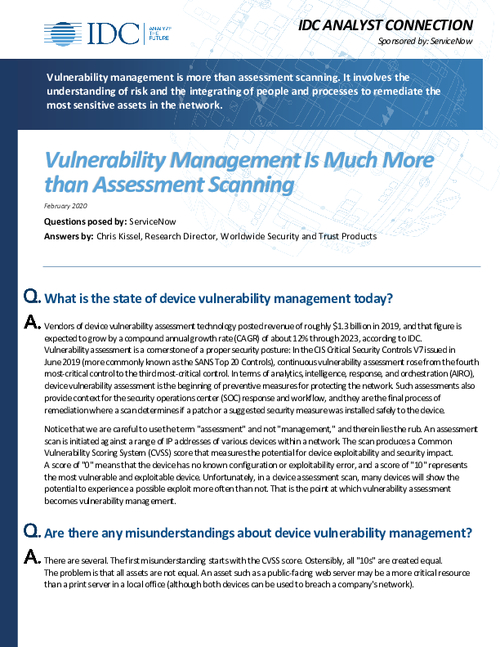
Sponsored by ServiceNow
IDC Analyst Connection: Vulnerability Management is Much More than Assessment Scanning
Sponsored by Anomali
The State of Threat Detection and Response from Anomali
Sponsored by GuidePoint Security
Delivering Business Value Through a Well-Governed Digital Identity Program
Sponsored by GuidePoint Security
Strategies for Building Cohesive Security Programs
Sponsored by Exabeam
A New Approach to Turbocharge Your Threat Detection and Response
Sponsored by Palo Alto Networks