Sponsored by Guidance Software
Sponsored by EdgeWave
Cyber Security Essentials for Banks and Financial Institutions
Sponsored by Experian
Data Privacy and Trust in the Mobile World
Sponsored by HP & Intel
Business Risk and the Midsize Firm: What Can Be Done to Minimize Disruptions?
Sponsored by Bit9
Data Theft Case Study: Learn From a Major Restaurant Chain
Sponsored by An Osterman Research White Paper, sponsored by DataMotion
Reduce Liability and Cost by Encrypting Content in Motion and at Rest
Sponsored by Good Technology
Union Bank Case Study: Securing Bank Data on Mobile Devices
Sponsored by DataMotion, Inc
Five Critical Questions Every Financial Institution Must Ask About Sending Sensitive Email
Sponsored by HP
HP Business Risk Mitigation Solutions with Disaster Recovery
Sponsored by nuBridges, Inc.
Protect Personally Identifiable Information (PII) as if Your Business Depends on It
Sponsored by DataMotion, Inc
Gain a Competitive Edge: A Case Study on Cloud-based Email Encryption Solutions
Sponsored by ThreatMetrix
Fraud Protection for Native Mobile Applications
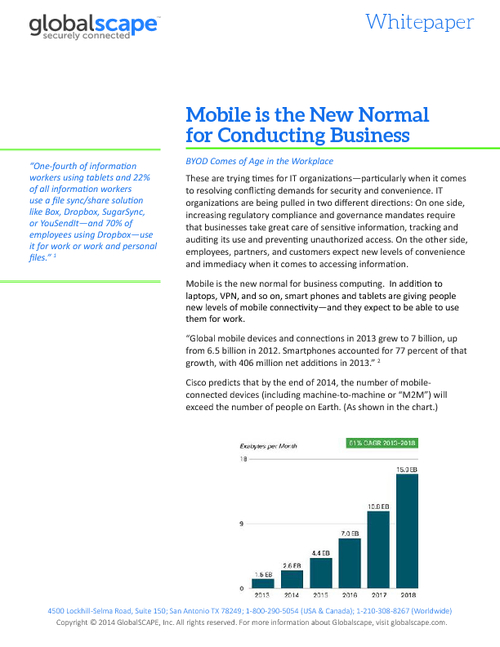
Sponsored by GlobalSCAPE
Mobile is the New Normal for Conducting Business
Sponsored by Symantec