Sponsored by CoreLight
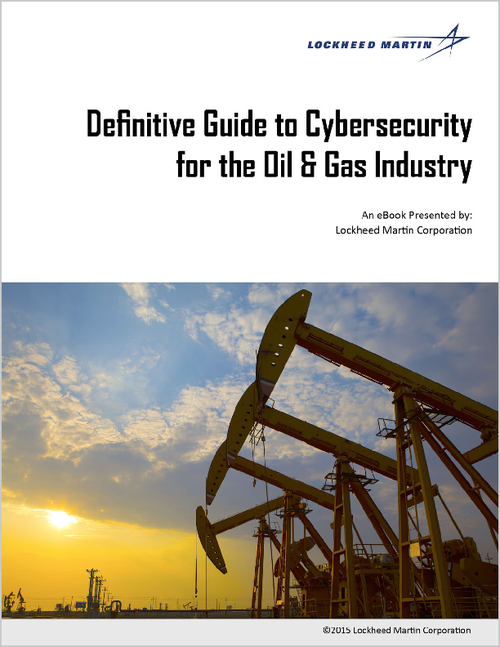
Sponsored by Lockheed Martin
Definitive Guide to CyberSecurity for the Oil & Gas Industry
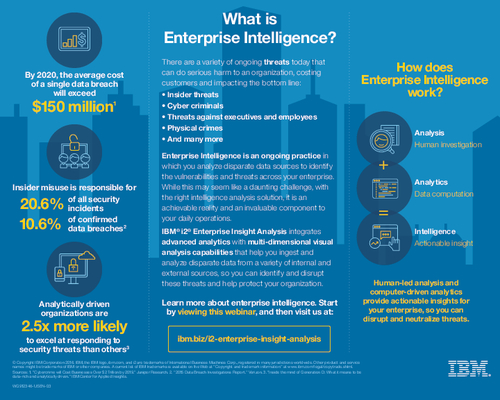
Sponsored by IBM
How Does Enterprise Intelligence Work?
Sponsored by IBM
Threat Intelligence Security Services Market Overview
Sponsored by IBM
Insider, Hacktivist or Nation State?
Sponsored by RSA
Best Practices to Improve Fraud Investigation
Sponsored by Rsam
4 Critical Elements of a Successful GRC Implementation
Sponsored by Rsam
7 Ways to Improve Your Security Incident Response
Sponsored by LogRhythm
How to Prevent High-Impact Cyber Incidents
Sponsored by LogRhythm
Simplify the the Federal OPSEC Mission with Security Intelligence
Sponsored by Bomgar
6 Steps to Secure Remote Access
Sponsored by Entrust Datacard
Top 5 Reasons Why Mobile will Transform Enterprise Authentication
Sponsored by Palo Alto Networks
Guidelines for AWS Hybrid Cloud Deployments
Sponsored by Palo Alto Networks