Sponsored by IBM
Content Enabling the Mobile Workforce
Sponsored by IBM
Could Your Content Be Working Harder and Smarter?
Sponsored by Good Technology
BYOD Policy Consideration: Security, Privacy, Acceptable Use and Expense
Sponsored by Good Technology
5 Critical Steps to Securely Manage Mobile Apps and Devices
Sponsored by Good Technology
Mobile App Security Using Containerization
Sponsored by Good Technology
Secure Mobility: Critical Container Requirements
Sponsored by IBM
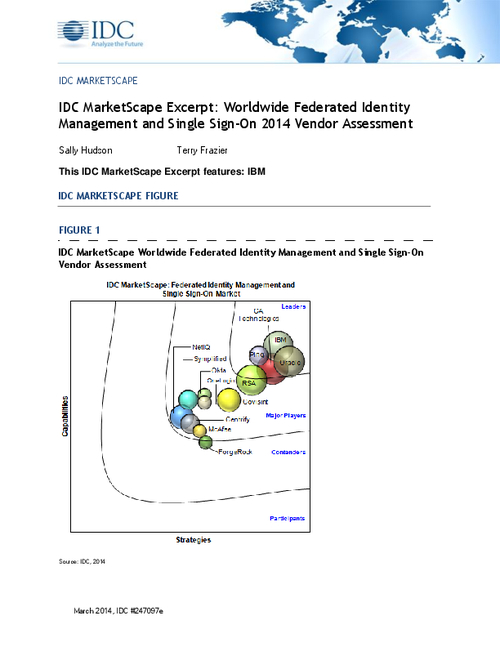
Worldwide Federated Identity Management and Single Sign-On
Sponsored by IBM
Consolidated Security Management for Mainframe Clouds
Sponsored by IBM
Mitigating Risks with Security Intelligence and Identity Assurance
Sponsored by IBM