Sponsored by Carbon Black
Sponsored by Carbon Black
Beyond the Hype: Artificial Intelligence, Machine Learning and Non-Malware Attacks Research Report
Sponsored by Malwarebytes
Barely 1 in 3 Global Organizations Prepared for Modern Cyberattacks
Sponsored by SentinelOne
The Future of AI and Machine Learning; A New Beginning for Endpoint Security Testing
Sponsored by IBM MaaS360
IBM MaaS360 with Watson - A cognitive approach to unified endpoint management
Sponsored by IBM MaaS360
Cognitive unified endpoint management with IBM MaaS360
Sponsored by IBM MaaS360
Unified management of endpoints, end users and everything in between
Sponsored by IBM MaaS360
Boost your mobile ROI with powerful Cognitive Insights
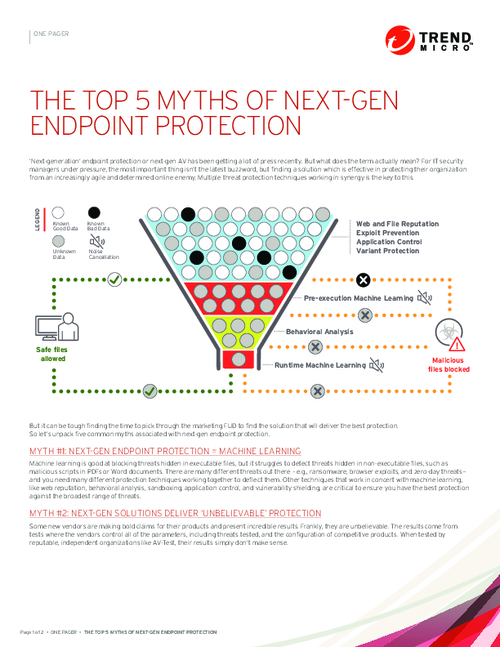
Sponsored by Trend Micro
There is No Silver Bullet: Why a Multi-layered Approach to Endpoint Security is a Must
Sponsored by Trend Micro
Beyond Next-gen: Defining Future-ready Endpoint Security
Sponsored by Fidelis
The First 72-Hours: How to Approach the Initial Hours of a Security Incident
Sponsored by Symantec
Endpoint Security: Creating Order from Chaos
Sponsored by FireMon
Improve Efficiency, Reduce Complexity: Firewall Cleanup Recommendations
Sponsored by SentinelOne
A New Approach to Endpoint Security Software Testing
Sponsored by Trend Micro