Sponsored by Cyberhaven
Sponsored by Cyberhaven
Addressing the Top 5 Gaps in DLP
Sponsored by Cyberhaven
Overcoming the Challenges of Data Classification
Sponsored by Picus Security
The Top 10 Most Prevalent MITRE ATT&CK Techniques
Sponsored by Palo Alto Networks
Global Investment Banking Firm Blazes New Trail to Remote Work with Complete Cloud-Delivered Security
Sponsored by Code42
Understanding your Insider Risk, and the Value of your Intellectual Property
Sponsored by Immersive Labs
eBook: Aligning Cyber Skills to the MITRE ATT&CK Framework
Sponsored by Abnormal Security
The Evolution of Ransomware: Victims, Threat Actors, and What to Expect in 2022
Sponsored by Pipl
4 Steps to Start Reducing False Declines
Sponsored by Pipl
How To Find & Deliver Trusted Approvals, Fast
Sponsored by Specops Software
5 Ways to Strengthen Your Active Directory Password Policy
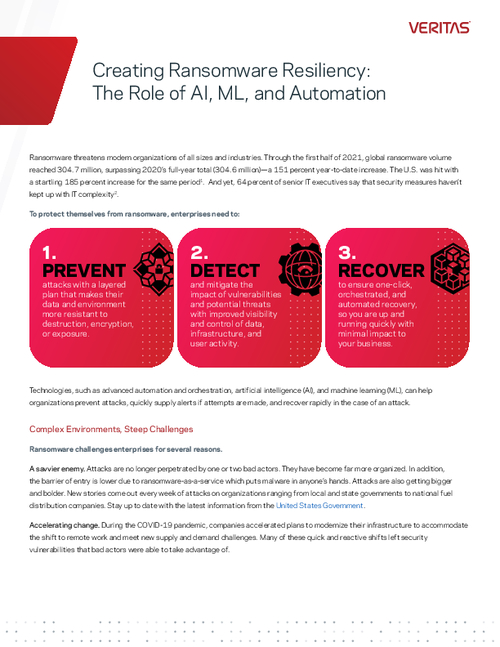
Sponsored by Veritas
Creating Ransomware Resiliency: The Role of AI, ML, and Automation
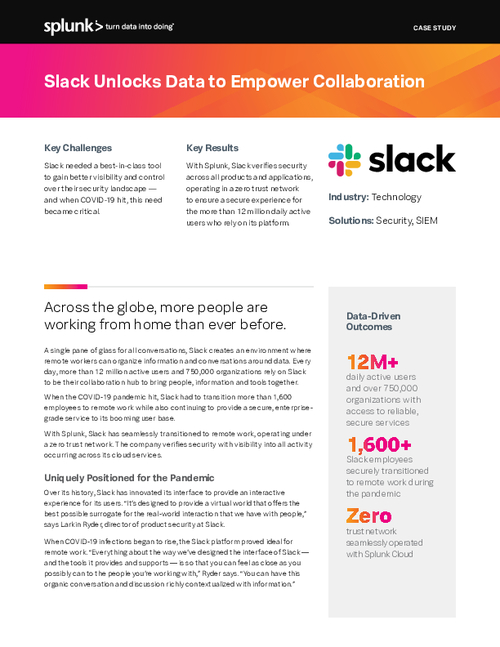
Sponsored by Splunk
Case Study: Slack Unlocks Data to Empower Collaboration
Sponsored by Splunk