Sponsored by Secure Code Warrior
Sponsored by Armis Security
Comprehensive Coverage for MITRE ATT&CK for ICS
Sponsored by Splunk
Financial Crime: The Rise of Multichannel Attacks
Sponsored by Gigamon
2020 Cyberthreat Defense Report
Sponsored by IronNet
Your Guide To Better Network Threat Detection
Sponsored by IronNet
AI for Cybersecurity: Hype or High Priority?
Sponsored by CyberGRX
Digital Transformation & Cyber Risk: What You Need to Know to Stay Safe
Sponsored by Security Compass
Cybersecurity Talent Shortage: Combining In-House Expertise With Automation
Sponsored by WatchGuard
Modernizing Midmarket Cybersecurity
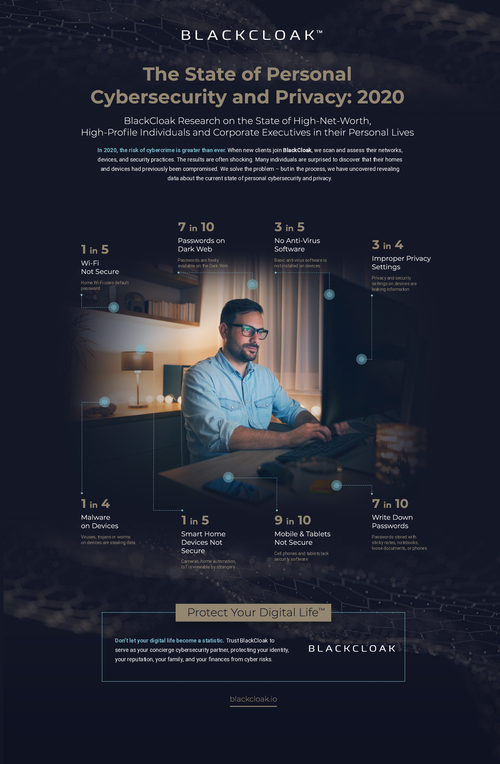
Sponsored by BLACKCLOAK
The State of Personal Cybersecurity and Privacy: 2020
Sponsored by BLACKCLOAK
Executive Protection at Home is the Major Gap in Cybersecurity
Sponsored by BioCatch
3 Ways Behavioral Biometrics Can Spot Criminals and Protect Customers
Sponsored by Radware
How to Keep APIs Secure from Bot Cyberattacks
Sponsored by IronNet
The Case for Collective Defense
Sponsored by SecureLink