Sponsored by BitSight
Sponsored by IBM
How to Use Behavioral Attributes & Cognition to Fight Fraud
Sponsored by Synchronoss
Healthcare's Unique Privacy Concerns: Where Does Security Fall Short?
Sponsored by AllClear
The Importance of Building a Customer-Obsessed Security Organization
Sponsored by Malwarebytes
2017 Security Predictions from Malwarebytes; New Year, New Threats
Sponsored by Forcepoint
Protecting Federal Agencies via Network Segmentation
Sponsored by Forcepoint
Millennials: A Tsunami of Risk for Federal Agencies?
Sponsored by Forcepoint
Rise Above the Risk: Privileged Users in the Federal Sector
Sponsored by Forcepoint
The New Digital Battlefield: 2017 Security Predictions
Sponsored by Forcepoint
Does Your NGFW Block 99.9% of Attacks, including AETs?
Sponsored by Preempt
Insider Threat: How to Spot Risky Behavior
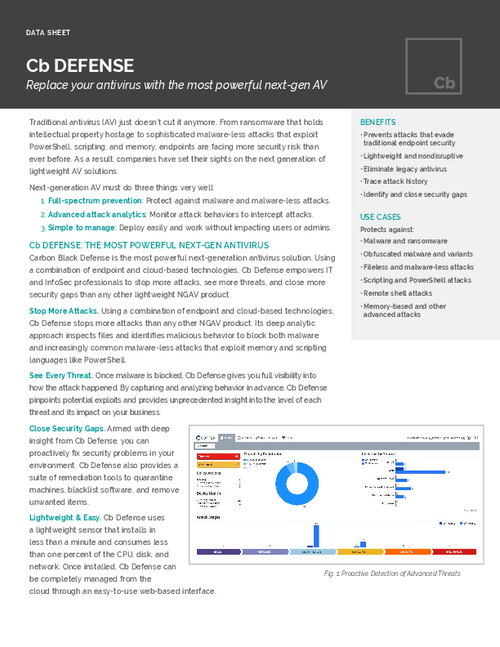
Sponsored by Carbon Black
Stop Attacks, See Threats, & Close Security Gaps with Next-Gen Anti-Virus
Sponsored by Recorded Future
The Six Core Competencies of a Successful Threat Intelligence Program
Sponsored by Malwarebytes