Sponsored by Proofpoint
Sponsored by HP
Work Smarter, Not Harder, to Secure Your Applications
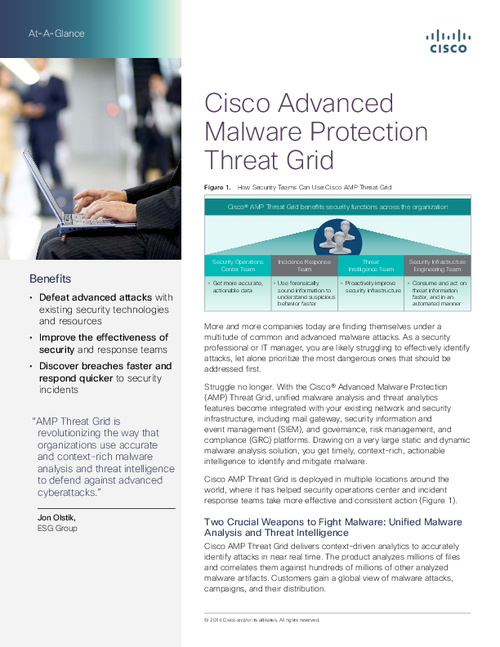
Sponsored by Cisco
Sustainable Security in a Constantly Changing Environment
Sponsored by Cisco
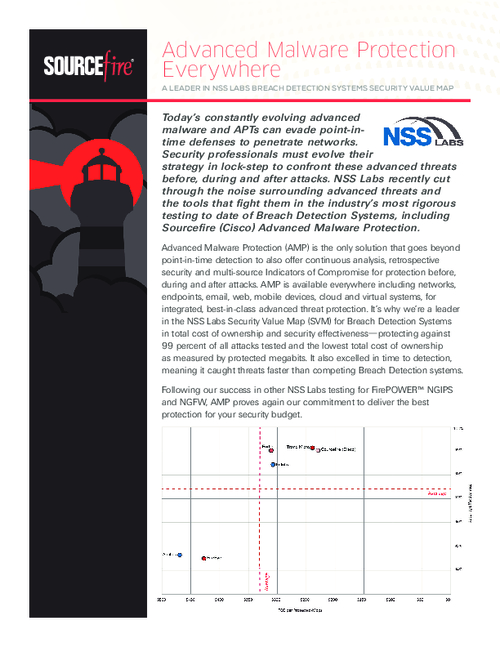
End-to-End Advanced Malware Protection
Sponsored by Cisco
Get Proactive with Advanced Malware Security
Sponsored by Cisco
FAQs Before Deploying Advanced Malware Protection
Sponsored by Cisco
2015 Annual Security Report
Sponsored by Prevoty
5 Reasons Hackers Love Your Application Security Strategy
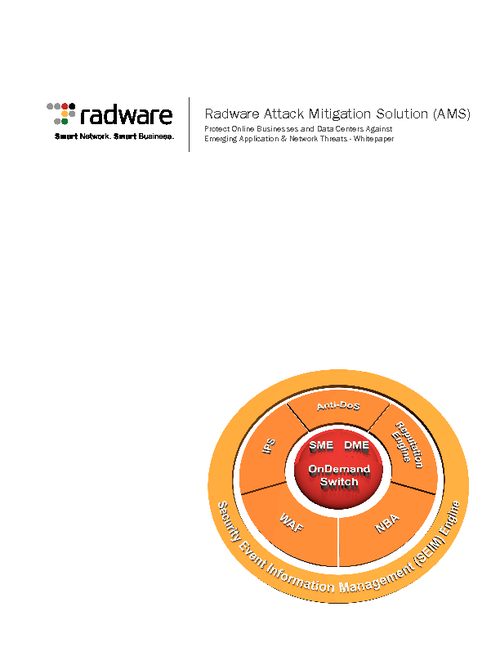
Sponsored by Radware
Global Application & Network Security Report
Sponsored by Sourcefire Network Security
Key Benefits of Application White-Listing and How to Achieve Them
Sponsored by Whitehat Security