Sponsored by Malwarebytes
Sponsored by Trend Micro
The Value of a Multi-layered Approach to Security
Sponsored by Malwarebytes
What You Should Expect From Malware in 2017
Sponsored by Malwarebytes
Top Cybercrime Tactics and Techniques; Attention-grabbing Threats in Q1 2017
Sponsored by Malwarebytes
Barely 1 in 3 Global Organizations Prepared for Modern Cyberattacks
Sponsored by LogRhythm
Analysis Report: OilRig Malware
Sponsored by Proofpoint
Best Practices for Dealing with Phishing and Ransomware
Sponsored by Fidelis
Is Next Generation Intrusion Prevention Right for You?
Sponsored by Fidelis
Phind the Phish - Reducing Phishing Detection from Months to Minutes
Sponsored by Fidelis
10 Impossible Things You Can Do with Metadata
Sponsored by Fidelis
The First 72-Hours: How to Approach the Initial Hours of a Security Incident
Sponsored by SentinelOne
A New Approach to Endpoint Security Software Testing
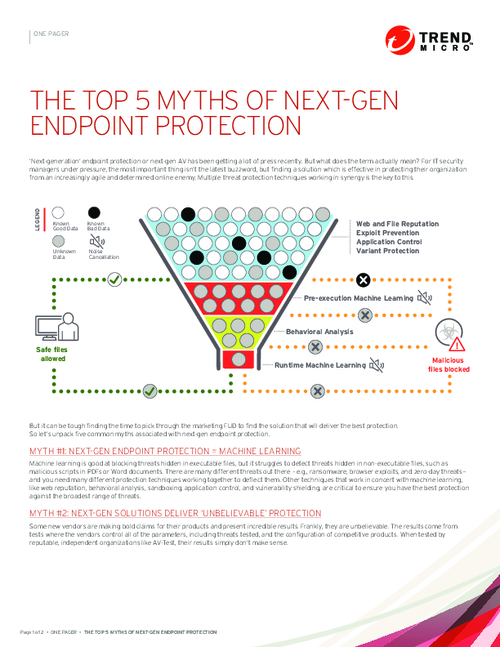
Sponsored by Trend Micro
The Top 5 Myths of Next-Gen Endpoint Protection
Sponsored by Trend Micro
Beyond Next-gen: Defining Future-ready Endpoint Security
Sponsored by Trend Micro