Cybercrime , Fraud Management & Cybercrime , Fraud Risk Management
Unusual Phishing Campaign Extracted Office 365 Credentials
Researchers: Fraudsters Used Combination of Techniques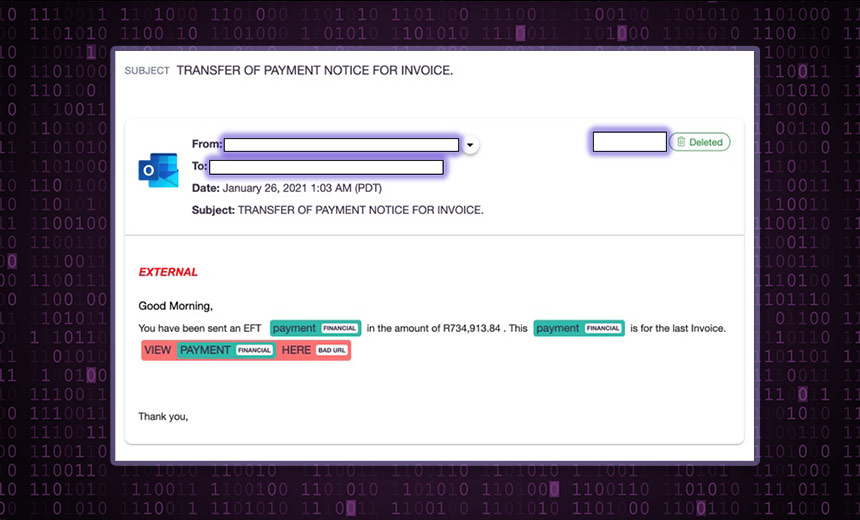
Security researchers at Armorblox uncovered an unusual invoice-themed phishing attack designed to extract victims' Microsoft Office 365 login credentials, alternate email addresses and phone numbers.
See Also: Disrupting the Secure Email Gateway: What is the Future of Email Security & Protection?
The campaign, which recently ended, struck about 20,000 accounts, Armorblox researchers estimate. The emails were branded with a Microsoft Outlook logo, had the subject line "Transfer of Payment Notice for Invoice" and purported to offer information about an electronic fund payment. The message portrayed a malicious HTML link as a way to view the invoice, the report, released Thursday, notes.
"This email attack bypassed native Microsoft email security controls. Microsoft assigned a Spam Confidence Level of '1' to this email, which meant that Microsoft did not determine the email as suspicious and delivered it to end-user mailboxes," says Rajat Upadhyaya, head of engineering at Armorblox.
The phishing campaign bypassed both Exchange Online Protection and Microsoft Defender for Office 365, the report says. The emails either skipped past spam filters or the security tool determined that they weren't spam, it says.
Clicking the Link
If a victim clicked on the malicious link in the phishing email, it sent the users through a redirect and landed on a page with the domain "mystuff[.]bublup[.]com." The redirect had the parent domain "nam02[.]safelinks[.]protection[.]outlook[.]com," which shows that the link was rewritten by native Microsoft security controls even though it was a malicious link, the report says.
Once on the new landing page, the victim was presented with a document named "Payment Notification - PDF" and a download icon. This was not an actual PDF document but an HTML file. When opened, it showed a new page branded with an Office 365 header and containing a single thumbnail file, the report says.
If a victim hovered the cursor over the file, which purported to be a PDF, they saw a Google Firebase link. Google Firebase is a platform designed to help people build mobile apps.
"Reputed URLs like that of Firebase will fool people - and email security technologies - into thinking that clicking the link will retrieve the invoice whose thumbnail is displayed," the report states.
If the recipient clicked on the thumbnail, a prompt appeared, requesting that the victim input their email address, email password and an alternative email address or phone number, the report says.
"This was an attempt by attackers to cover their bases in case victims have two-factor authentication or recovery mechanisms set up on their Microsoft accounts," Upadhyaya says.
At this point, the malware took an unusual turn, according to the researchers. If the victim typed in fake or incorrect login credentials, the page reset and asked the user to enter the correct information.
"This might point to some back-end validation mechanism in place that checks the veracity of entered details," the report states. "Alternately, attackers might be looking to harvest as many email addresses and passwords as possible and the error message will keep appearing regardless of the details entered."
'Uniquely Sophisticated'
Upadhyaya says the combination of techniques made this campaign unusual.
"The individual techniques from this attack have been employed by hackers before, but it's the combination of techniques that makes the attack uniquely sophisticated and enabled it to bypass Microsoft email security as well as pass victims' eye tests," he says.
Although the phishing campaign has ended, the fraudsters have kept the domains used during these attacks active, Armorblox reports.