Cybercrime , Fraud Management & Cybercrime , Social Engineering
Tax-Themed Phishing Campaign Emerges
Hackers Try to Use Remote Access Trojans to Take Control of Devices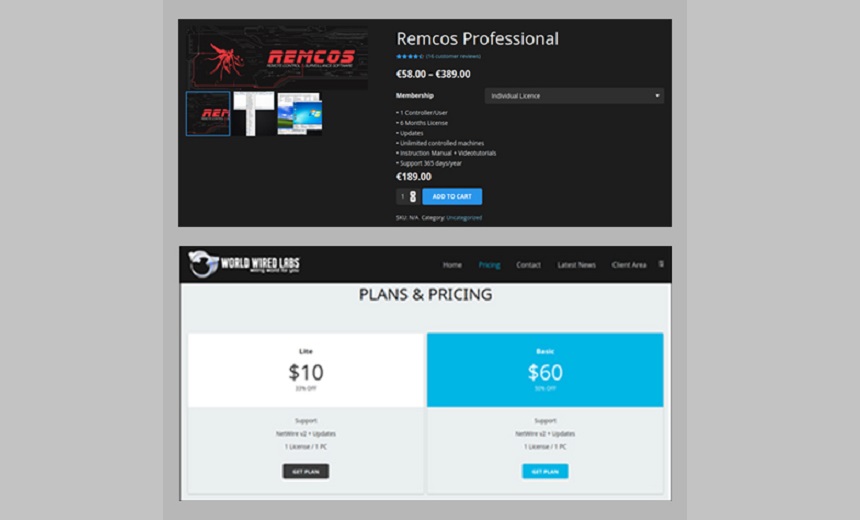
This tax season, as in years past, a major phishing campaign is targeting U.S. taxpayers in an effort to deliver malware, according to researchers at security firm Cybereason.
See Also: OnDemand | A Master Class on Cybersecurity: Roger Grimes Teaches Data-Driven Defense
The phishing messages contain malicious documents that purport to contain tax-related content but ultimately deliver NetWire and Remcos remote access Trojans that enable hackers to take control of victims’ devices, the researchers say. The malware has file and system management capabilities.
The campaign, which is designed to evade antivirus tools, tricks victims into opening the tax-themed Word document containing a malicious macro that downloads an OpenVPN client on the targeted machine.
"The malware dropper establishes a connection to the legitimate cloud service 'imgur' and downloads the NetWire or Remcos payloads by way of steganography, where the malicious code is hidden within an innocuous looking jpeg image file," Cybereason reports.
Seasonal Campaigns
Paul Norris, senior systems engineer at security company Tripwire, says that each year, hackers leverage the urgency of the tax filing deadline to ramp up their phishing efforts.
"This is because phishing campaigns are much more successful when the message creates a sense of urgency in the recipient, who is more likely to download an attachment or click on a link without thinking twice," Norris notes.
Ciaran Byrne, head of platform operations at the security company Edgescan, says this campaign appears to be taking a scattergun approach, using common malware delivery techniques and pushing out messages to a large number of potential victims.
In February, the Internal Revenue Service issued a warning about fraudsters spoofing the agency's domains and incorporating its logos and language into phishing campaigns (see: IRS Warns of Fresh Fraud Tactics as Tax Season Starts).
Attack Analysis
In the latest campaign, if the recipients of a phishing message open what's portrayed as a tax-themed Word document, it displays a blurred background as well as “enable editing” and “enable content” prompts, Cybereason says.
"This is a known social engineering method used to encourage the user to enable embedded macros to run on their machine," the researchers note. "Once the malicious content is being executed, an embedded and heavily obfuscated macro is run on the victim’s machine."
The malware payload is eventually dropped in the users “Temp” directory, and the DLL is injected into Notepad and continues the infection chain. This DLL includes a loader for Remcos or NetWire.
"Upon execution, the payload method starts decrypting data using a XOR key," the researchers note. "The first decrypted part is an additional executable code, and the second part is decrypting the URL the loader connects to in order to download the next execution stage."
Once decryption is complete, the malicious code is injected into a “tracert.exe” that downloads the OpenVPN client along with a trojanized DLL file called “libcrypto-1_1.dll”, which is side-loaded to the OpenVPN client upon execution, Cybereason says.
"It further creates a persistence for the VPN client by creating automatic execution of a .lnk file," the report states. "The malicious code in the sideloaded DLL unpacks an additional DLL in-memory and injects it into 'notepad.exe.' A secondary payload hidden in an image file is then downloaded from 'imgur.com,' a cloud image storage service. The decrypted payload can be either NetWire or Remcos."
Assaf Dahan, senior director and head of threat research at Cybereason, says the use of steganography, storing payloads on legitimate cloud-based services and exploiting DLL sideloading against legitimate software makes these campaigns very difficult to detect.
“The sensitive information collected from the victims can be sold in the underground communities and used to carry out all manner of identity theft and financial fraud,” Dahan states.
The NetWire and Remcos remote access Trojans used in this campaign are available on crime forums for as little as $10 per month via the malware-as-a-service model, Cybereason reports.