Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development , Ransomware
Scottish Hospitals Hit by Bitpaymer Ransomware
New Variant of Crypto-Locking Ransomware Evaded Defenses
Hospitals in Lanarkshire, Scotland, are continuing to recover following a recent outbreak of ransomware known as "Bitpaymer."
See Also: Cybersecurity Checklist: 57 Tips to Proactively Prepare
"We quickly identified the source of the malware and investigations are ongoing as to how this was able to infiltrate our network," says Calum Campbell, chief executive of the board that oversees NHS Lanarkshire.
NHS Lanarkshire - part of Britain's National Health Service - comprises three major hospitals and 13 community hospitals in southern Scotland.
After the ransomware was discovered, NHS Lanarkshire immediately issued a public alert via Facebook on Aug. 25, warning that "the staff bank system" - referring to temporary workers - "and telephone are offline and currently unavailable."
Later that day, the medical director for its acute division urged patients to avoid seeking care at the emergency department "unless it is essential."
By Aug. 26, however, concerns appeared to have eased. "We would ask patients who are attending hospital or out-of-hours services over the weekend to bear with us as they may experience longer ... waits than usual," the health board warned in a weekend update.
NHS Lanarkshire was also one of the victims of the WannaCry ransomware outbreak in May.
NHS Lanarkshire says the ransomware used in this attack is a new variant of Bitpaymer, aka Bit Paymer, and that its IT security team is continuing to review how the malware was able to evade the organization's defenses. It says most affected systems were restored after IT teams worked around the clock over the weekend.
"NHS Lanarkshire did not pay any ransom," a spokesman tells Information Security Media Group.
He adds that the malware evaded in-place anti-virus defenses. "Our security software and systems were up to date with the latest signature files, but as this was a new malware variant, the latest security software was unable to detect it," the spokesman says. "Following analysis of the malware, our security providers issued an updated signature so that this variant can now be detected and blocked."
NHS Lanarkshire says a small number of scheduled procedures and appointments had to be canceled as a result of the malware outbreak.
"Our staff have worked hard to minimize the impact on patients and our contingency plans have ensured we have been able to continue to deliver services while the IT issues were resolved. A small number of systems were affected, with the majority restored over the weekend and the remainder on Monday," according to its chief executive, Calum Campbell.
"I would like to apologize to anyone who has been affected by this disruption," he says. We immediately started work to reappoint patients to the earliest possible appointments."
Bitpaymer Ransomware
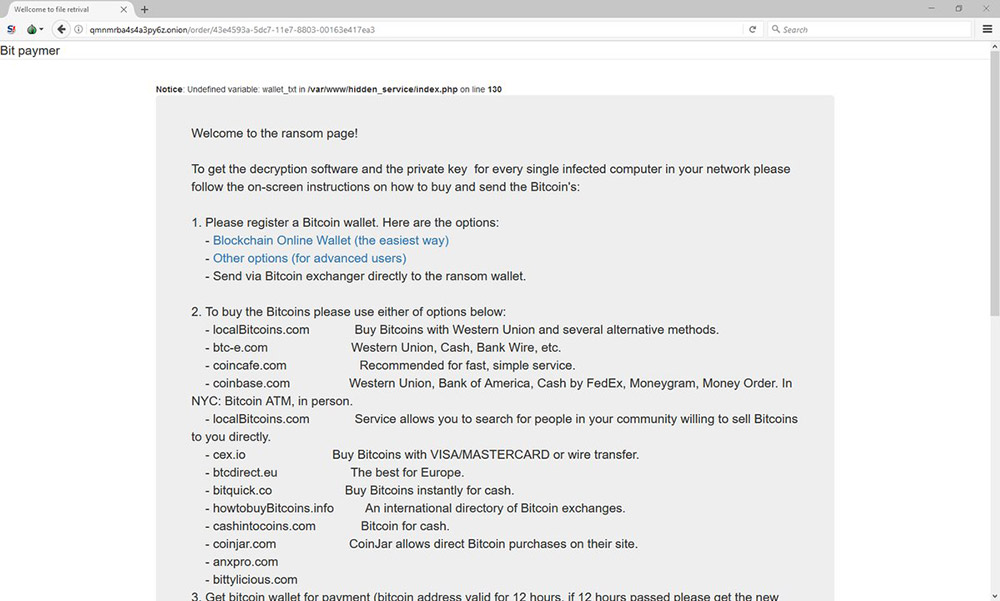
After infecting a system, Bitpaymer saves a crypto-locked version of numerous file types, adding a ".locked" extension to the filename, according to malware researcher Michael Gillespie, aka @demonslay335, who's part of the ID-Ransomware project.
Sometimes, ransomware developers make mistakes when writing their code or attempting to enable the crypto-locking features that replace a victim's files with encrypted versions. In such cases, security researchers can often reverse the crypto and release free decryption tools for victims (see Two New Ransomware Decryptors Give Victims a Free Out).
Unfortunately, files infected by Bitpaymer ransomware are encrypted using the RC4 and RSA-1024 encryption algorithms in a way that cannot be cracked, Gillespie reports.
Confirmed Bitpaymer #ransomware is not decryptable. CryptGenRandom RC4 per file + RSA-1024. Thanks for analysis @FraMauronz https://t.co/TUpzYUDbhT
— Michael Gillespie (@demonslay335) July 14, 2017
Of course, victims can pay attackers in exchange for the promise of a decryption key. But security and law enforcement experts urge victims to never do so, warning that it funds further cybercrime (see Please Don't Pay Ransoms, FBI Urges).
A ransomware researcher at security firm Emsisoft who goes by xXToffeeXx or @PolarToffee says Bitpaymer is often spread via remote desktop protocol - RDP - attacks, which involve attackers gaining remote access to PCs or servers via RDP client software or protocols, "usually with very high ransom demands."
Indeed, according to security firm Enigma Software, some Bitpaymer ransomware infections demand 50 bitcoins as a ransom payment. With bitcoin's current sky-high value, that would be worth more than $235,000.
Brute-Force RDP Attacks
Bitpaymer is just one of hundreds of different types of ransomware being tracked by security experts.
And ransomware that spreads via attackers brute-forcing RDP credentials is "very, very common," England-based security researcher Kevin Beaumont, aka "GossiTheDog," says via Twitter. "I track RDP ransomware, it's big business."
In February, Trend Micro security researcher Jay Yaneza described how these types of brute-force RDP attacks work in a blog post devoted to a strain of ransomware called Crysis.
Yaneza says attackers find an internet-connected endpoint with RDP enabled. "The attacker tries to log in using various commonly used usernames and passwords," he writes. "Once the attacker has determined the correct username and password combination, he (or she) usually comes back multiple times within a short period to try and infect the endpoint. These repeated attempts are usually successful within a matter of minutes."
In one case, for example, Trend Micro researchers found that a single endpoint had been infected with six Crysis infections - each packed a different way, to fool signature-based detection - in just 10 minutes. "The attackers had multiple files at their disposal, and they were experimenting with various payloads until they found something that worked well," Yaneza says.
He cautions that it's up to IT security teams to ensure that they've locked down any endpoint on which RDP is enabled and urges them to try and find any enterprise IP addresses on which unprotected RDP is in operation. "With newer versions of Windows, the OS logs Remote Desktop connection details in the Windows Event Viewer with the Event ID 1149," he notes. "The logged information includes the user account that was used (i.e., the compromised account), as well as the IP address of the attacker."
As that suggests, some RDP attacks are very targeted. "The interesting thing about Bitpaymer is that they are specifically targeting companies, and not just any companies, quite big companies," xXToffeeXx tells anti-malware site Bleeping Computer. "This is quite different to most other RDP company targeting ransomware. Reminds me of SamSam" (see South Korean Hosting Firm Pays $1 Million Ransom).
New Campaign: 20 Million Attack Attempts
But many ransomware campaigns continue to rely on volume rather than careful targeting.
For example, a separate ransomware campaign has been sending spam emails to attempt to trick recipients into opening a malicious JavaScript attachment stored in a 7zip-format archive, according to security, networking and storage vendor Barracuda Networks.
"In the last 24 hours, the Barracuda advanced security team has observed about 20 million attempts at a ransomware attack through an email attachment 'Payment_201708-6165.7z,'" Eugene Weiss, lead platform architect for Barracuda Networks, says in a blog post.
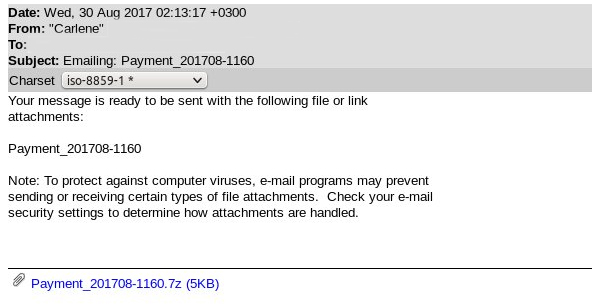
"In this attack, the source of the email is a spoofed address, and the attachment name and number is included in the subject line and body of the message," he adds. "The full subject line in this example is 'Emailing: Payment_201708-6165' and the number in the attachment name is variable."
Security experts say the best way to defend against all ransomware attacks is to run up-to-date anti-malware software as well as maintain current, offline backups, so that affected systems can be wiped and restored.
Update (September 1): Added comment from NHS Lanarkshire that it did not pay any ransom.