Cybercrime , Cybercrime as-a-service , Fraud Management & Cybercrime
REvil Ransomware Suspects Snared in Global Police Crackdown
Arrests and Indictments Tied to Attacks Against Kaseya, State of Texas and Others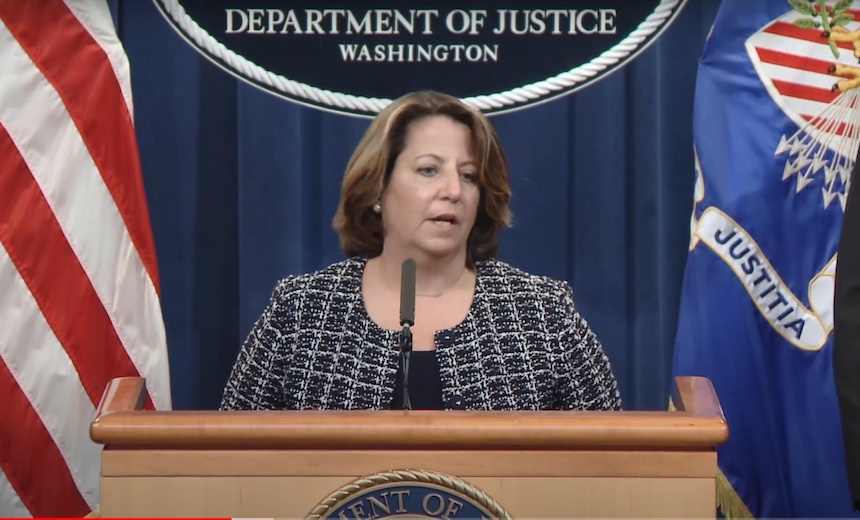
The U.S. Department of Justice on Monday announced that one Ukrainian man has been arrested and a Russian man indicted for launching devastating ransomware attacks against numerous targets. Both are accused of being affiliates of the REvil - aka Sodinokibi - ransomware operation, and their alleged targets included the software company Kaseya and multiple Texas municipalities.
Earlier on Monday, European law enforcement officials separately announced the arrest of multiple other business partners of Sodinokibi as well as its predecessor operation, which was called GandCrab.
See Also: Take Inventory of Your Medical Device Security Risks
The arrest and indictments are the latest salvo to be launched by a multinational law enforcement effort as governments around the world continue to crack down on ransomware, which continues to seriously disrupt numerous businesses, school districts, hospitals and more. The U.S. and many other nations have vowed to bring increased law enforcement as well as intelligence agency resources to bear on tracking down ransomware-wielding perpetrators.
"Our message to ransomware criminals is clear: If you target victims here, we will target you," said Deputy Attorney General Lisa Monaco at a Monday press conference. "The Sodinokibi/REvil ransomware group attacks companies and critical infrastructures around the world, and today's announcements showed how we will fight back."
Europe's law enforcement agency, Europol, says six more suspected participants tied to GandCrab or REvil have also now been arrested, thanks to the combined efforts of police in Australia, Belgium, Canada, France, Germany, the Netherlands, Luxembourg, Norway, Philippines, Poland, Romania, South Korea, Sweden, Switzerland, Kuwait, the United Kingdom and the United States.
Kaseya Attack Suspect Arrested in Poland
Justice Department officials Monday said one suspected member of REvil, Ukrainian national Yaroslav Vasinskyi, 22, was arrested on Oct. 8 in Poland. The U.S. is now seeking his extradition.
A federal indictment unsealed Monday charges Vasinskyi with multiple attacks, including against Miami-based IT managed service software provider Kaseya. In that attack, REvil was used to infect about 1,500 customers of dozens of Kaseya-using managed service providers. Ransoms were demanded from each individual victim to decrypt their systems, although the attacker brazenly also offered to sell Kaseya a single, "universal decryptor" to unlock every system for $70 million.
While the Kaseya attack was massive in scale, officials said the FBI was able to move quickly to assist victims, thanks to quick action by the software company.
"In their darkest hour, Kaseya made the right choice," Monaco said. "Almost immediately after they were hit, Kaseya provided the FBI information they needed to act."
The FBI somehow was able to obtain the decryption key for the strain of REvil that was used against Kaseya. How exactly it did so has not been revealed, and the FBI has been criticized after reports emerged that it withheld the key for several weeks as part of a bigger effort to disrupt REvil, which didn't go according to plan when the group suddenly disappeared on July 13.
But FBI Director Christopher Wray said during the Monday press conference that having the key did enable the bureau to help multiple victims of the Kaseya attack decrypt their data.
Wray also urged Congress to pass mandatory breach-reporting legislation so that law enforcement agencies can get real-time data about ransomware and any ransoms paid. If a victim does opt to pay a ransom demand, which will be via virtual currencies such as Bitcoin or Monero, Wray said that immediately alerting law enforcement agencies increases the likelihood that investigators can seize those funds before criminals attempt to move them between cryptocurrency wallets to launder the proceeds.
Monaco told reporters that the FBI stands ready to immediately assist victims. "If you pick up the phone and if you call the FBI, this team is waiting for you on the other end of the line," she said.
Suspect Charged With Attacking Texas
U.S. officials Monday also announced the indictment of Russian national Yevgeniy Polyanin, 28, who remains at large. Polyanin has been charged with running multiple REvil ransomware attacks.
One of his alleged victims was TSM Consulting Services Inc., which is a small IT services provider that manages systems on behalf of others. In 2019, TSM was hit with REvil ransomware and used as a springboard to infect systems used by its clients, which included 22 Texas municipalities' systems.
The DOJ also announced that it has seized from Polyanin cryptocurrency worth $6.1 million that he received in ransom payments. Monaco says the seizure was facilitated by "good, old-fashioned detective work," and that "we were able to recover ransom by following the money."
Europol Details Operation GoldDust
Also on Monday, Europol, the EU's law enforcement agency, announced that globally, multiple GandCrab and REvil-using suspects - collectively tied to about 7,000 ransomware infections globally and hundreds of millions of dollars in ransoms paid by victims - have been arrested since February.
"All these arrests follow the joint international law enforcement efforts of identification, wiretapping and seizure of some of the infrastructure used by Sodinokibi/REvil ransomware family, which is seen as the successor of GandCrab," Europol says.
The arrests are part of a 17-nation-strong operation codenamed GoldDust, aimed at disrupting the infrastructure, operators and affiliates of REvil. The effort is being coordinated by Europol; Eurojust, which is the EU's criminal justice cooperation agency; and Interpol.
Beyond Vasinskyi's detention in Poland, further arrests have happened in Asia, Europe and the Middle East:
- South Korea: In February, April and October, South Korean police arrested three suspected affiliates of the GandCrab and Sodinokibi/REvil ransomware families, tying the suspects to 500 known victims.
- Romania: On Thursday, local police arrested two suspected REvil affiliates, allegedly tied to 5,000 infections and $580 million in ransom payments received.
- Kuwait: Local police Thursday arrested a suspected GandGrab affiliate.
Insights, intelligence and cooperation from private security firms Bitdefender, McAfee Enterprise and the security team at Dutch telecommunications giant KPN have been a crucial component in the GoldDust operation, Europol says.
"We provided technical analysis of not only the ransomware, but identified key REvil infrastructure, identified suspects and provided tooling that allowed law enforcement to extract configurations from malware samples," John Fokker, the principal engineer and head of cyber investigations for Advanced Threat Research at McAfee Enterprise, tells Information Security Media Group.
Working with an unnamed law enforcement agency, Romanian firm Bitdefender in September released a free decryptor for all REvil attacks that occurred before July 13. The company had previously released free decryptors for multiple strains of GandCrab.
"Since mid-September this year, the Sodinokibi/REvil decryptor has helped more than 1,400 companies in 83 countries recover their files and save over $550 million in unpaid ransom," Bogdan Botezatu, director of threat research at Bitdefender, says in a blog post.
From GandCrab to REvil
GandCrab first appeared in January 2018. Later that year, Romanian investigators launched a multinational effort, backed by Europol and including the participation of the U.S., the U.K. and others, to target that cybercrime operation, which ultimately counted more 1 million victims worldwide.
REvil debuted in April 2019, about a month before GandCrab disappeared. Both operations offered ransomware-as-a-service to affiliates, who would take the crypto-locking malware developed by the operators and use it to infect victims. For every victim who paid a ransom, the typical arrangement was that an affiliate would receive a 70% cut, with the rest going to the core operators.
Security experts say some core members of GandCrab, as well as affiliates, went on to work with REvil, which dominated the ransomware landscape. Ransomware incident response firm Coveware says that of the thousands of incidents it investigated from April through June, REvil was the most prevalent strain of crypto-locking malware tied to those attacks.
REvil-wielding attackers demanded an average ransom of $393,000, which was "much higher than GandCrab's average ransom of between $800 and $2,400," Bitdefender's Botezatu says in a blog post.
Did REvil Overreach?
But REvil's longevity may have been threatened not only by launching high-profile and highly disruptive attacks in the West, but also scamming its own affiliates. Earlier this year, malware reverse-engineering specialists on the Russian-language Exploit cybercrime forum analyzed REvil samples and reported finding a backdoor that could be used by administrators to decrypt systems and files encrypted using the malware. Those findings, which were reported by threat-intelligence firm Advanced Intelligence, were interpreted as REvil's developers having given themselves a backdoor so they could negotiate directly with victims, while pretending to the responsible affiliate that the victim had declined to pay.
The Exploit reverse-engineering specialists reported that the backdoor was present until REvil disappeared in July, and no longer present when it reappeared in September. The operation went offline again in October, after one of its administrators, 0_neday, reported that the group's Tor-based victim-naming site and payment portal had been hijacked.
REvil or its affiliates hit Brazilian meat processing giant JBS in May, which netted them a ransom worth $11 million. In the wake of that attack, and the July 2 hit on Kaseya, the White House announced increased efforts to disrupt and deter ransomware operations.
Since this past summer, REvil's infrastructure has been targeted and disrupted by U.S. Cyber Command and an unnamed foreign government, according to reports published by Reuters and The Washington Post. Those disruptions appear to have driven at least some core members of the operation to cease working with the group, in part due to concerns that they might be unmasked by police.
Ransomware Attacks Surge On
The latest arrests show police taking a bite out of cybercrime, by arresting multiple ransomware operation affiliates.
"The FBI has worked creatively and relentlessly to counter the criminal hackers behind Sodinokibi/REvil," FBI Director Wray said Monday. "Ransomware groups like them pose a serious, unacceptable threat to our safety and our economic well-being. We will continue to broadly target their actors and facilitators, their infrastructure, and their money, wherever in the world those might be."
Nevertheless, many criminals continue to use ransomware in innovative new ways, drawn by the easy profits and relatively safety afforded by such schemes, especially for individuals based in countries such as Russia, which never extradites citizens to face crimes allegedly committed against foreign targets.
"Kudos to the team for the degree of collaboration and expertise demonstrated in bringing about these arrests - keep watching that space," says Alan Woodward, a visiting professor of computer science at the University of Surrey, via Twitter. "Sadly it's far from game over - the operation against these ransomware groups is ongoing."
Indeed, Coveware reports that many former REvil affiliates appear to have already migrated to rival operations Conti and LockBit 2.0.
Executive Editor Jeremy Kirk contributed to this report.