Fraud Management & Cybercrime , Social Engineering
Recent Spear-Phishing Attacks Originate From Legit Accounts
Researchers: Fraudsters' Domains Created to Steal Office 365 Credentials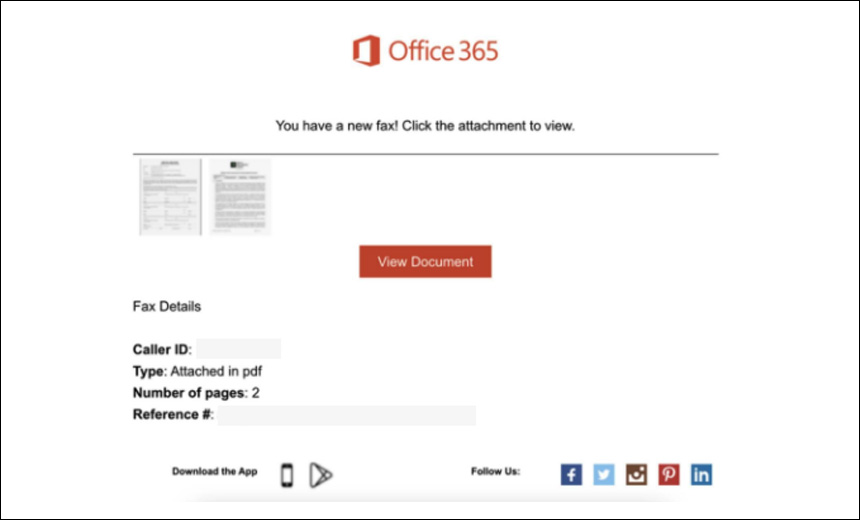
A spear-phishing campaign detected earlier this month that uses messages that appear to originate with legitimate companies is targeting enterprise users in an effort to steal Microsoft Office 365 credentials, according to a report from Abnormal Security.
See Also: Live Webinar | Human Detection & Response: Exploring Three Security Awareness Realities
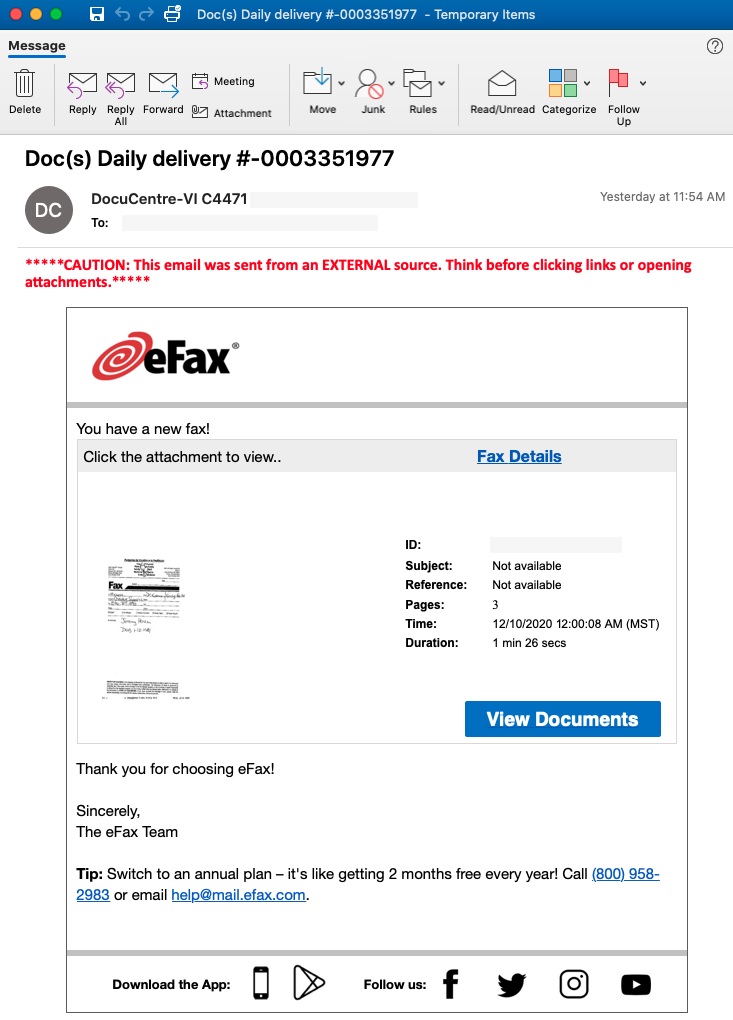
The fraudsters appear to have compromised hundreds of legitimate accounts to help craft realistic-looking emails, the researchers say. In one case, the malicious messages impersonated eFax, an online fax service, and the messages included personalized "Doc Delivery" notifications to entice victims to click.
The phishing emails typically contain an embedded link that leads the user to what the researchers call “never-seen-before Microsoft Office 365 spear-phishing pages hosted on legitimate digital publishing sites such as Joom, Weebly and Quip.” So far, hundreds of these domains have been detected, according to the report.
If security tools detect a phishing email that is part of the campaign, the fraudsters deploy a script that will change the address of the impersonated sender so the attacks can continue.
"The widespread use of hundreds of compromised accounts and never-seen-before URLs indicate the campaign is designed to bypass traditional threat intelligence solutions accustomed to permitting known but compromised accounts into the inbox," according to the Abnormal Security report.
Phishing Emails
The report notes that many of the phishing emails in this campaign impersonate legitimate businesses and services and originate from compromised accounts, which the researchers did not list.
In the case of the eFax email, the fraudsters appear to use legitimate logos and artwork from the company, and the message even contains language about how users can switch plans or email for help.
The use of the compromised email accounts to send these messages is a way to bypass security tools and filters, such as secure email gateways.
"While this may seem counterintuitive on the attackers’ part to send an eFax notification from an unrelated compromised account, it's a clever tactic by the attackers and problematic for the organization because compromise attacks will bypass traditional threat intelligence-based solutions," the Abnormal Security researchers say. "The reason the bypass works is because the compromised email addresses are known and trusted by the organization based on prior and legitimate communications."
Malicious Link
If the phishing email is opened, the user is presented with a "View Documents" link embedded in the message. This leads to a domain hosted on the Joom, Weebly or Quip landing page, and the victim is then asked to click another link.
"The attacker attempts to legitimize the campaign with official-looking landing pages similar to those used by eFax," according to the report.
If clicked, the second link directs the victim to the final phishing domain and asks the user to input their Office 365 credentials, which are then harvested by the fraudsters.
Other Phishing Scams
Abnormal Security researchers also uncovered another phishing campaign that also was designed to steal Office 365 credentials. These emails appeared to originate with the victim's IT department and asked about migrating to a new Outlook version (see: Phishing Campaign Uses Outlook Migration Message).
In November, Microsoft's Security Intelligence team warned Office 365 users about a phishing campaign that appeared to be harvesting victims' credentials (see: Microsoft Warns of Office 365 Phishing Attacks).