Business Continuity Management / Disaster Recovery , Fraud Management & Cybercrime , Fraud Risk Management
Ransomware Newcomers Include Pay2Key, RansomEXX, Everest
Maze May Have Exited, But Fresh Gangs Arrive Bearing Dedicated Data-Leaking Sites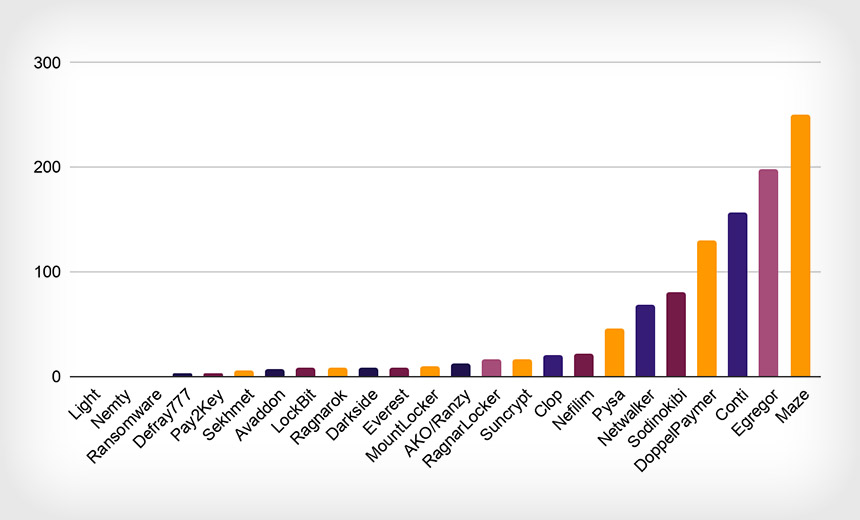
While the Maze ransomware gang retired last year, new operators emerged, using crypto-locking malware to extort victims.
See Also: Cybersecurity for the SMB
The newer ransomware players include Pay2Key, RansomEXX and Everest, according to security firms that track cybercrime operators.
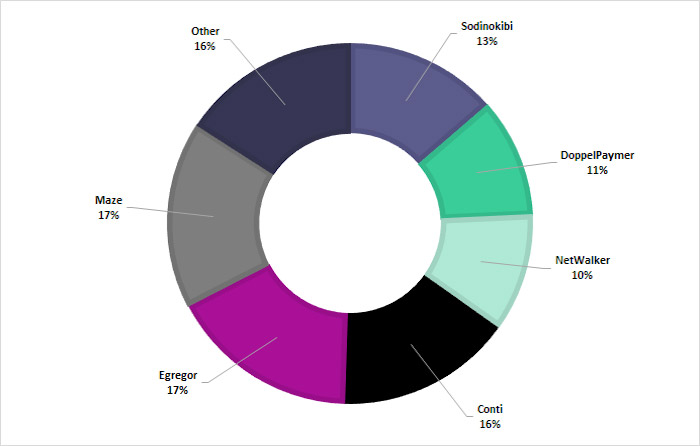
But many of the big operators continue their campaigns. Furthermore, just six ransomware operations - Maze, Egregor, Conti, Sodinokibi/REvil, DoppelPaymer and NetWalker - were responsible for 84% of all known attacks last year, says San Francisco-based digital risk protection firm Digital Shadows.
The company says the other 16% of attacks were waged by 14 other operations: Ako/Ranzy Locker, Avaddon, Clop, DarkSide, Everest, LockBit, Mount Locker, Nefilim, Pay2Key, PYSA, Ragnar Locker, RansomEXX, Sekhmet and SunCrypt.
From Q3 to Q4 last year, the average ransom payment declined by 34%, reaching $154,108, while the median ransom payment dropped by 55% to $49,450, reports ransomware incident response firm Coveware, based on thousands of cases it investigated. While experts have hailed the decline, they also note that the volume of ransomware attacks and ransom payments flowing to attackers remains substantial.
Pay or Face Leaks
To help maximize their profits, the 20 ransomware operators identified by Digital Shadows all run dedicated data-leaking sites, where operators can list victims in a "name and shame" attempt to force them to pay. If that doesn't work, many groups escalate to leaking data, followed by dumping all stolen data, to try to pressure future victims into paying to avoid a similar fate.
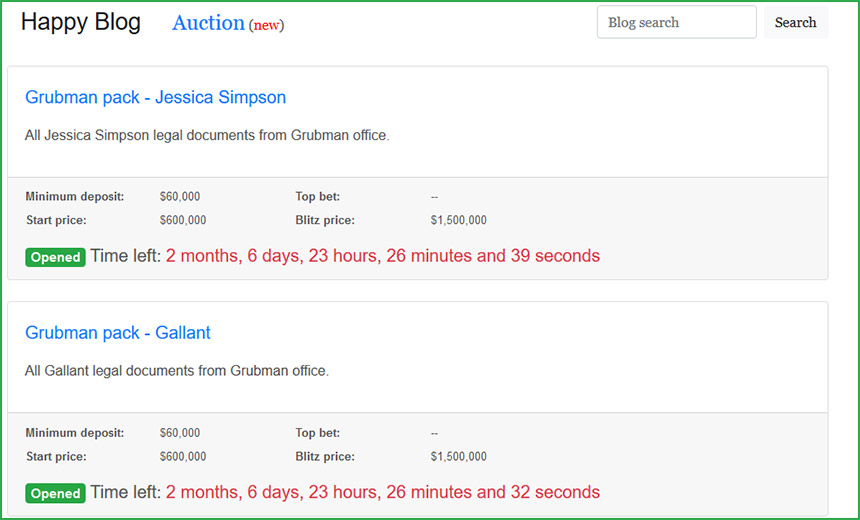
Digital Shadows dubs this the "pay or get breached trend" - although arguably, at least some of the targeted organizations have already been breached and had their data exposed. Such data exposure could trigger data breach notification requirements of U.S. state laws or the EU's General Data Protection Regulation. Some gangs are also demanding one or more payments for a promise to delete stolen data or to refrain from selling it to other crime gangs.
"'Pay or get breached' is the term we use for the double extortion method," says Jamie Hart, a cyber threat intelligence analyst at Digital Shadows. But just because a group claims to have stolen data, that doesn't mean the gang actually did so, she notes.
The security firm Coveware, for example, reports seeing a rise toward the end of 2020 of attackers fraudulently claiming to have stolen data before they crypto-locked systems.
But many ransomware gangs do now exfiltrate data. "The majority of the posts on data leak sites include a link or a screenshot of information as a sample, but prior to the data being posted on the site, there is no indication the data has been accessed beyond the bulk of data being exfiltrated from a victim organization's network," says Digital Shadows' Hart. "If a company pays the ransom, presumably the data is deleted, and no one sees it. Without a payment, the data is then exposed, and an official data breach has occurred as the information is publicly available."
Law enforcement officials continue to urge organizations to never pay a ransom, but instead to devote more resources to defense and disaster recovery. With proper disaster recovery measures in place, organizations can wipe and restore systems without having to contemplate giving money to criminals in exchange for the promise of a decryption tool or a pledge to stop leaking stolen data.
Crossover Belies Size of Ransomware Market
But business is booming for ransomware-wielding gangs, bolstered by the success of the ransomware-as-a-service model, in which operators provide crypto-locking malware to affiliates, who hack systems and deliver the malware. Ransomware operators and their affiliates share in any profits from subsequent ransom payments.
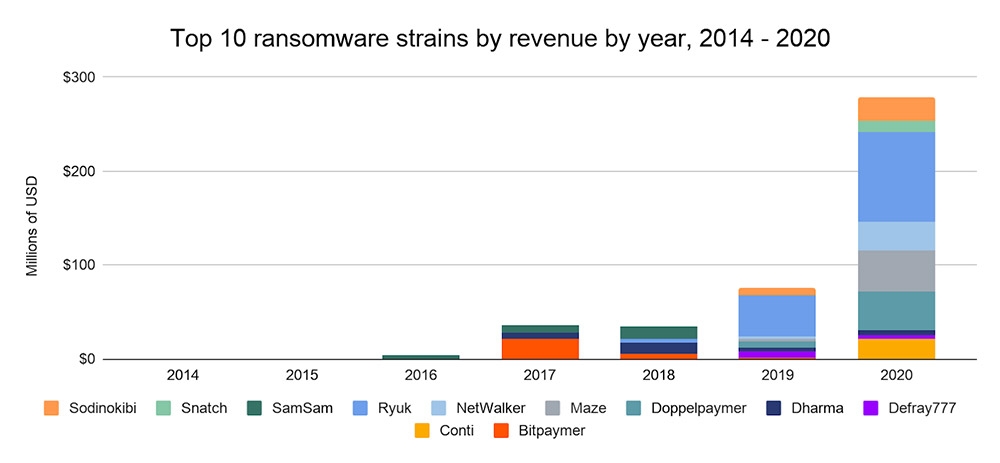
One quantitative wrinkle when analyzing ransomware operations, however, is that many criminals cross over between multiple programs, for example, as affiliates of different ransomware-as-a-service programs, says blockchain analysis firm Chainalysis.
"The number of strains active throughout the year may give the impression that there are several distinct groups carrying out ransomware attacks, but this may not be the case," Chainalysis says. "Many RaaS affiliates migrate between strains, suggesting that the ransomware ecosystem is smaller than one might think at first glance. In addition, many cybersecurity researchers believe that some of the biggest strains may even have the same creators and administrators, who publicly shutter operations before simply releasing a different, very similar strain under a new name."
Opportunistic Attacks - Except for Geography
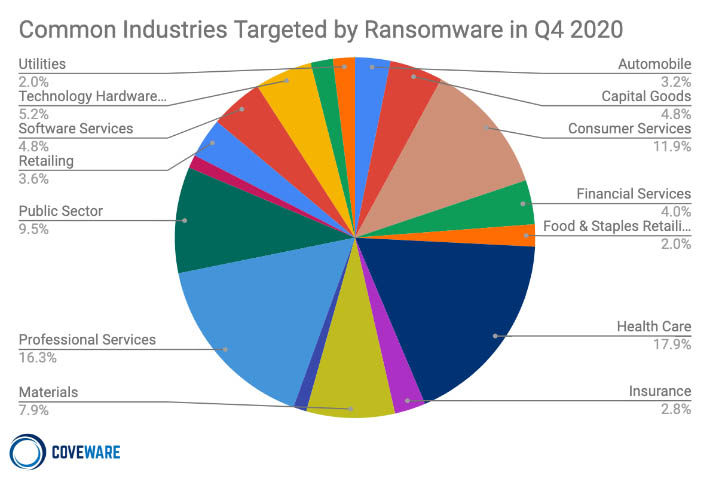
From a victim-selection standpoint, at least in aggregate, ransomware operators appear to be opportunists. Last year, attackers appeared to hit anything they could, without any apparent bias. Nearly one-third of last year's known attacks hit the industrial goods and services sector, followed by construction at 9%, technology at 8%, retail at 7% and legal services at 5%, according to Digital Shadows' reading of victims named on data-leaking sites or news reports.
Coveware, meanwhile, says that of the thousands of cases it was hired to help investigate in Q4 2020, the majority involved healthcare, followed by professional services, consumer services and the public sector.
Geographically speaking, however, attackers most often hit North American targets. Last year, the region accounted for 66% of known ransomware attacks, followed by Europe at 23% and Asia at 3%, Digital Shadows says.
Threat intelligence firm Flashpoint notes that for the 1,100 attacks described on gangs' data-leaking sites from November 2019 through the end of 2020, 56% involved U.S. victims, followed by Canada at 7%, France and the U.K. at 5%, Germany at 4% and Italy at 3%.
Different ransomware strains may have a different geographical focus.
"Even though some ransomware groups will target specific countries or regions - e.g., Everest ransomware victims are primarily based in Canada, Clop focuses on Germany, and Ragnarok targets are largely from countries in southeast Asia - when it comes to industry vertical, attackers are relatively agnostic, allowing opportunity to dictate ransomware organization victims and targets," Flashpoint says.
Tracking the Operations
Which ransomware operations are most active continues to change.
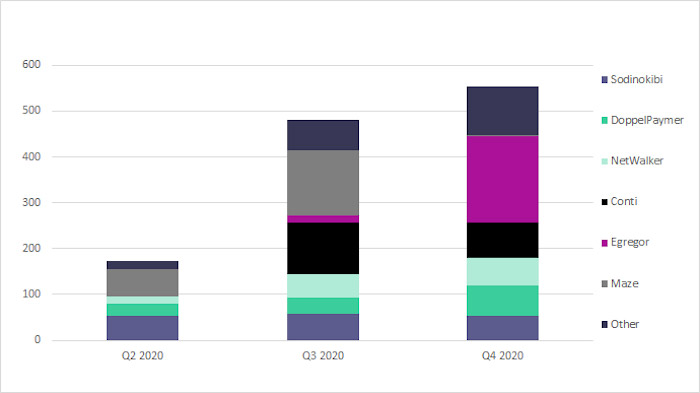
In Q3 of last year, for example, 76% of Digital Shadows' data-leaking ransomware alerts were tied to Maze, Conti, Sodinokibi and NetWalker.
But in Q4 2020, "activity decreased" for Sodinokibi - aka REvil, and Maze on Nov. 1 announced it would be ceasing operations. For all of Q4, Egregor, Conti, NetWalker, and DoppelPaymer accounted for 71% of all alerts, Digital Shadows says.
Experts say Egregor appears to have seized Maze's mantle, and it may also have picked up its affiliates.
In the meantime, ransomware has already rocketed into 2021, driven by RaaS operations - except, perhaps, for Netwalker, which was the focus of a law enforcement operation that this month resulted in the arrest of a suspected member of the group in Canada.
Unfortunately, ongoing technical and business innovation by ransomware-wielding criminals has been driving more victims to pay. So much so that as Emsisoft warned at the end of last year: "Unless significant action is taken, we anticipate 2021 being another banner year for cybercriminals."
As ransomware continues to generate massive profits for criminals, why would they ever stop using it?