COVID-19 , Cybercrime , Fraud Management & Cybercrime
Phishing Campaigns Leverage Latest COVID-19 Themes
Researchers Issue Warnings After Malicious Messages Tied to Economic Stimulus Plans Surface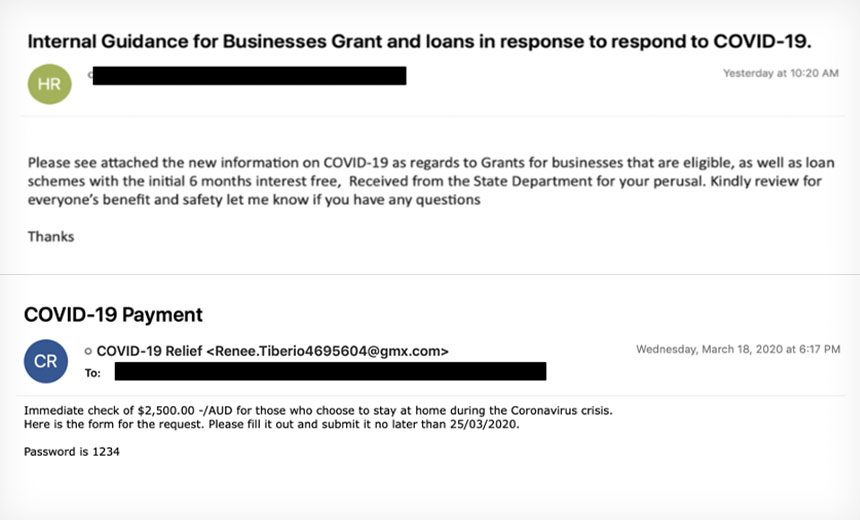
With the U.S. and other nations adopting economic stimulus packages as a result of the global COVID-19 pandemic, fraudsters are now using the promise of government checks as phishing lures to spread banking Trojans, according to a pair of new security research reports.
See Also: The State of Organizations' Security Posture as of Q1 2018
Researchers at FireEye and IBM X-Force report that fraudsters already are attempting to take advantage of the $2 trillion U.S. stimulus package that Congress passed last week and that President Donald Trump signed into law Friday as a lure for malicious messages. For example, they’re sending phishing emails disguised as information about stimulus checks, unemployment compensation and small business loans, researchers say.
The researchers note that many of these spam and phishing emails are attempting to lure victims into downloading a banking Trojan that FireEye calls SilentNight and IBM refers to as Zeus Sphinx. The malware, also referred as Zloader and Terdot, has been in use by cybercriminals for at least a decade (see: Zeus Banking Trojan Spawn: Alive and Kicking).
"While some Sphinx activity we detected trickled in starting December 2019, campaigns have only increased in volume in March 2020, possibly due to a testing period by Sphinx’s operators," according to the IBM report released Monday. "It appears that, taking advantage of the current climate, Sphinx's operators are setting their sights on those waiting for government relief payments."
Both IBM and FireEye spotted some version of these scams targeting victims in the U.S., Canada, Australia and other countries that have rolled out or are preparing economic stimulus plans.
COVID-19-Themed Frauds
Since COVID-19 was first spotted in China in January, cybercriminals, fraudsters and even some nation-state hackers have used public fears about the disease to spread phishing emails, spam and malware. As of Tuesday morning, there had been over 800,000 confirmed cases of COVID-19 around the world, and more than 39,000 deaths related to the disease, according to Johns Hopkins University.
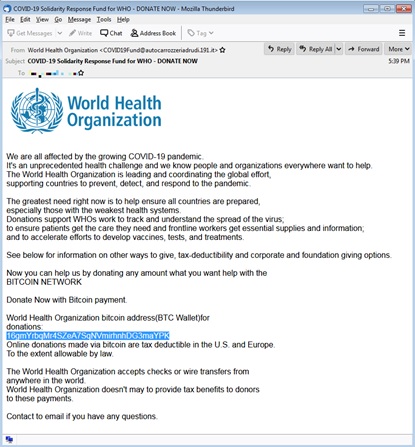
On Tuesday, security firm Trustwave released an analysis of several phishing email campaigns using COVID-19 as a lure. These included spoofed messages from the World Health Organization that purport to offer updates on the pandemic but contain malware and infostealers, as well as highly targeted malicious messages written in Italian. Italy has been hard hit by the pandemic.
New Targets
In the latest round of phishing emails that IBM analyzed, the messages use the promise of financial compensation related to COVID-19 as a lure. The email comes with an attached document, typically a .doc or .docx file, which is designed to look like a questionnaire that needs to be filled out in order to receive the money, according to the report.
If the victim opens up the attached document and enables macros, a downloader is activated, which then calls to a command-and-control server to deliver the Zeus Sphinx malware to the infected device, according to the IBM report. The malware then hides itself in different files and avoids anti-virus software by using a self-signed certificate, the report notes.
Once Zeus Sphinx maintains persistence within the infected device, the malware will then use a web injection within a browser - it can affect Firefox, Chrome and Internet Explorer - when the user visits certain websites, such as online banking sites, according to the report.
"It calls on its [command-and-control] server to fetch relevant web injections when infected users land on a targeted page and uses them to modify the pages users are browsing to include social engineering content and trick them into divulging personal information and authentication codes," IBM reports.
Other Attacks
FireEye researchers encountered a similar campaign targeting Canadian organizations starting around March 18. Phishing emails were sent with an attached Microsoft Word document, called "COVID 19 Relief.doc." If opened, malicious macros helped install the Silentnight banking Trojan, which infects devices in much the same way as the Zeus Sphinx malware does, according to the report.
In addition to phishing emails attempting to deliver banking Trojans, the FireEye researchers found another campaign using messages that appear to come from the U.S. Small Business Administration with the subject line: "Internal Guidance for Businesses Grant and loans in response to respond to COVID-19," according to the report.
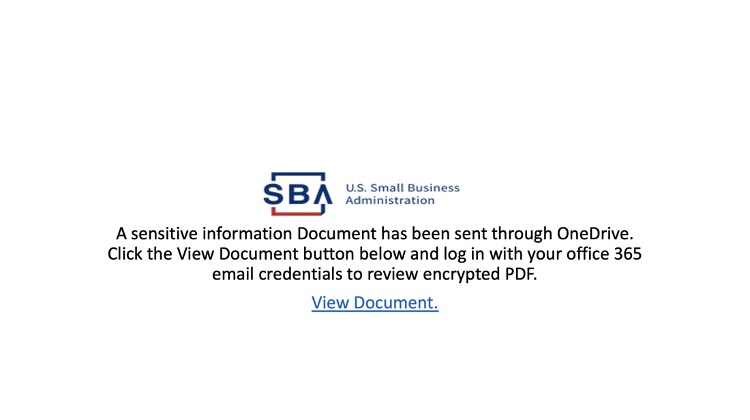
The FireEye report finds that these phishing emails lead to a spoofed Microsoft Office sign-in page that attempts to trick victims into inputting their credentials, which are then harvested and sent back to the attackers.
More of these types of phishing and spam campaigns are inevitable, FireEye reports.
"Although campaigns employing themes relevant to these matters are only beginning to be adopted by threat actors, we expect future campaigns - primarily those perpetrated by financially motivated threat actors - to incorporate these themes in proportion to the media’s coverage of these topics," FireEye says.
COVID-19 Attacks By the Numbers
Since the outbreak of COVID-19 in January, the amount of spear-phishing emails using the pandemic as a lure has skyrocketed, according to an analysis by Barracuda Networks.
Of the more than 467,000 spear-phishing emails that Barracuda researchers analyzed between March 1 and March 23, more than 9,100 included a COVID-19 theme as a lure, or about 2 percent of the total, according to the report. In February, the number of COVID-19 phishing emails totaled 1,180 and only 137 of these messages were detected in January, according to the report.
"Goals of the attacks ranged from distributing malware to stealing credentials, and financial gain. One new type of ransomware our systems detected has even taken on the COVID-19 namesake and dubbed itself CoronaVirus," according to the Barracuda report.























