Business Continuity Management / Disaster Recovery , Fraud Management & Cybercrime , Governance & Risk Management
Microsoft Debunks DoppelPaymer Ransomware Rumors
Infections Spread Not Via Microsoft Teams, But By Stolen Active Domain Credentials
For workers who prefer that their chat-based workspaces not be used as ransomware-distribution vectors, worry not. But for anyone responsible for safeguarding Active Directory, stay on alert.
See Also: Mandiant Cyber Crisis Communication Planning and Response Services
So says Microsoft, which on Wednesday moved to counter what it says have been ongoing rumors suggesting that DoppelPaymer ransomware was being distributed via its cloud-based Teams communication and collaboration platform, as well as via the BlueKeep vulnerability in Windows remote desktop protocol.
"Our security research teams have investigated and found no evidence to support these claims," Dan West and Mary Jensen - respectively the senior security program managers for all of Microsoft and for the Microsoft Security Response Center - say in newly issued customer guidance about DoppelPaymer ransomware.
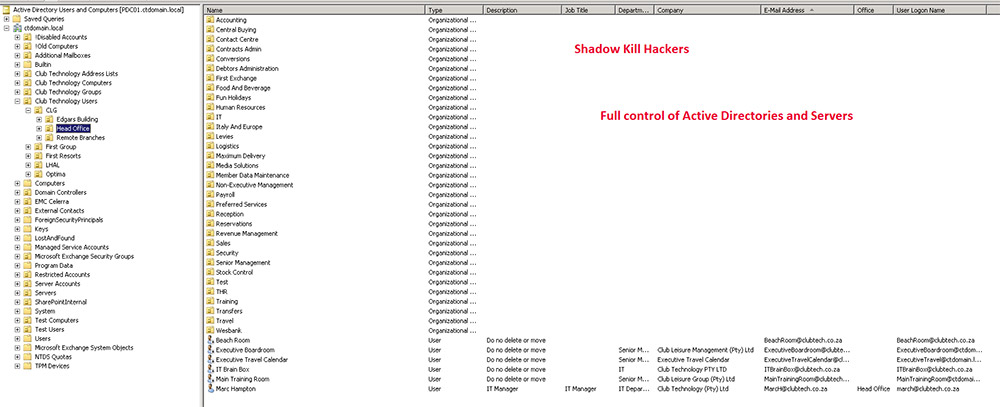
"In our investigations, we found that the malware relies on remote human operators using existing domain admin credentials to spread across an enterprise network," they say. Domain admin refers to members of an Active Directory group that by default have full control of the domain, which is why such credentials can be targeted by attackers (see: Why Hackers Abuse Active Directory).
So while BlueKeep poses a risk to organizations, and many organizations have yet to patch it, so far it hasn't been tied to ransomware distribution (see: Microsoft Warns Users: Beware of Damaging BlueKeep Attacks).
But as West and Jensen note, attackers are continuing to abuse Windows networks and protocols to spread ransomware, including via Active Directory.
DoppelPaymer Pummels Victims
DoppelPaymer appears to be a variant of BitPaymer ransomware, which has been used to extort ransoms of $25,000 to $1.2 million, according to cybersecurity firm CrowdStrike. Like many types of ransomware, victims must use a Tor-based payment portal to pay any ransoms, it says.
Whereas BitPayer largely targeted European organizations, since DoppelPaymer first appeared in June, it's been used to hit targets across North and South America, from Chile to Texas, CrowdStrike says.
One recent victim was Mexico's state-run oil company Permex, which received a ransom demand worth about $5 million in bitcoins but has refused to pay .
Target: Active Directory
Permex hasn't described how attackers cracked its network. But criminal abuse of AD for spreading ransomware is a likely culprit; such abuse is widespread and nothing new.
Earlier this year, for example, aluminum giant Norsk Hydro was hit by a highly targeted LockerGoga ransomware attack after hackers used the firm's Active Directory services to distribute crypto-locking code to endpoints (see: Hydro Hit by LockerGoga Ransomware via Active Directory).
Criminals continue to use ransomware as a way to monetize their ability to gain remote access to enterprise networks, often by buying cracked or stolen RDP credentials. But security experts say that ransomware is often only the final stage of a longer attack that begins with network penetration, continues through to the theft of intellectual property and other valuable data - especially for customers or payment card data - and culminates with a crypto-locking code outbreak (see: Ransomware Gangs' Not-So-Secret Attack Vector: RDP Exploits).
"Globally, ransomware continues to be one of the most popular revenue channels for cybercriminals as part of a post-compromise attack," Microsoft's West and Jensen say. "They tend to target enterprise environments through methods like social engineering, enticing an employee to click a link to visit an infected site, and opening downloaded or emailed infected documents and programs on their computers."
Some criminal groups have been launching more targeted attacks, gaining access via RDP, using Windows tools such as Powershell to move laterally within victims' networks and using Mimikatz to harvest passwords, including for domain administrators (see: Texas Ransomware Responders Urge Remote Access Lockdown).
So while Microsoft has debunked the use of Teams or BlueKeep as mechanisms for spreading DoppelPaymer, the technology giant used the rumors to issue a renewed call to arms. "Security administrators should view this threat as additional motivation to enforce good credential hygiene, least privilege and network segmentation," West and Jensen say. "These best practices can help prevent DoppelPaymer operators and other attackers from disabling security tools and using privileged credentials to destroy or steal data or hold it for ransom."
Repeat Ransomware Distribution Mechanism
Huy Kha, an information security professional at a Dutch law firm who's an expert on Active Directory security, says too many firms continue to fail to lock down their Windows environments, which can give attackers an edge to use against them. That's despite the vast majority of businesses today using Active Directory as their domain network management tool of choice (see: Essential Active Directory Security Defenses).
"Active Directory remains crucial for most organizations around the world, and one of the common reasons why it is so easy for attackers to subvert is because too many organizations continue to manage AD like they did 10 years ago," Kha tells Information Security Media Group. "Attackers have been bypassing the network perimeter for years. Traditional network defenders need to step up their game by assuming they have been breached, as a first principle, and working from there to further secure and lock down their environment."
One recent example: The city of Johannesburg, which was exploited via Active Directory last month by a group calling itself Shadow Kill Hackers, which demanded 4 bitcoins - worth about $34,000 at the time - in exchange for a decryptor. Despite the attackers threatening to dump stolen data if they weren't paid, the city has vowed to not pay (see: Johannesburg Struggles to Recover From Ransomware Attack).
Lockdown Guidance
Huy says that while Microsoft has issued detailed instructions to customers for locking down Active Directory when used with its Azure cloud computing environment, it's done less well with standalone Active Directory security guidance. "Microsoft could help customers out with providing clear guidance like they did with Azure," he says, pointing as an example to recommendations for managing administrator roles in Azure Active Directory released by Microsoft in March.
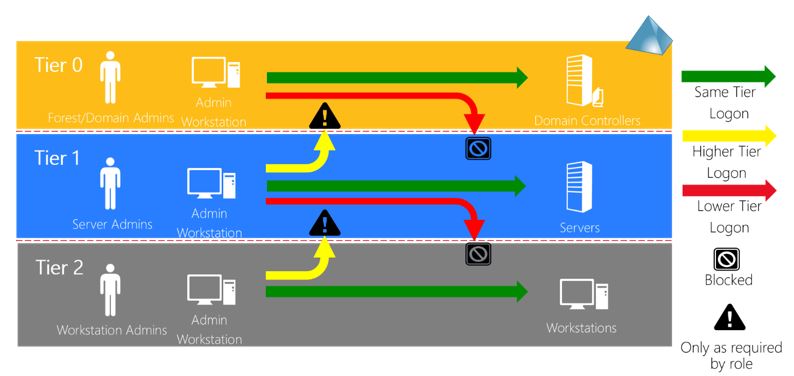
Whatever organizations do, less access means better security, and even when greater access might be temporarily required, it should be downgraded as soon as possible. "Enforcing least-privilege access is difficult, but absolutely not impossible," Kha says. "I do encourage people to do this, and I hope that most organizations understand that domain or enterprise admin tasks, such as promoting a domain controller, upgrading a domain functional level, installing an entire Exchange set-up, deploying Azure AD Connect or adding a new domain trust might require you to temporarily elevate domain/enterprise admin privileges, but that doesn't mean you always need it."
Kha also recommends locking down Azure AD Connect, as well as certificate authority servers, for example, by placing them into the most restricted level of access - tier 0, per Microsoft's model. "Attackers don't necessarily need to compromise your domain controller. They also can attack your Azure AD Connect and CA servers to gain access. So those are great examples of the types of servers that you should always put into tier 0."