Critical Infrastructure Security , Cybercrime , Cyberwarfare / Nation-State Attacks
Hackers Breached Israeli Water Reservoir HMI System
Researchers Say Attack May Have Links to Iran, But Lacked Sophistication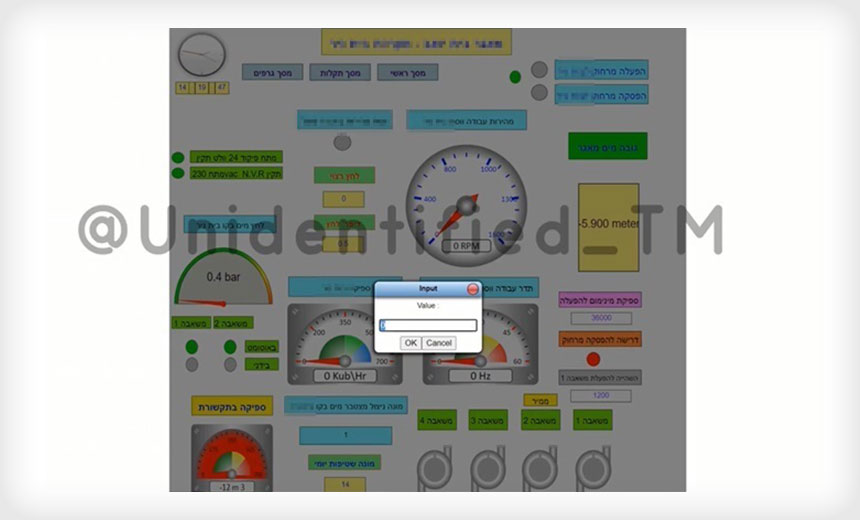
Hackers with possible links to Iran appear to have breached an unprotected human-machine interface system at an Israeli water reservoir that connected directly to the internet and lacked security protocols, according to industrial cybersecurity firm Otorio.
See Also: 10 Incredible Ways You Can Be Hacked Through Email & How To Stop The Bad Guys
The security firm reports that the alleged Iranian hacking group, referred to as "Unidentified TEAM," published a video of the attack on an unnamed reclaimed Israeli water reservoir human-machine interface (HMI) system, which did not require any authentication to access and modify the system. This allowed the threat actors to tamper with the water pressure, change temperatures and more.
"All the adversaries needed was a connection to the world-wide-web, and a web browser," the researchers note in a report.
An HMI is a user interface or dashboard that connects a person to a machine, system or device and is mainly used in the context of an industrial process. In May, security firm Trend Micro released a report that noted HMI systems used in "smart factories" were susceptible to hacking (see: 'Smart' Factories Could Face Unique Attacks: Report).
A video reportedly showing breach was posted Dec. 1 on Unidentified TEAM's Telegram channel. The group is also believed to have attacked U.S. websites.
In the Telegram post, the hacking group stated they targeted the Israeli water reservoir firm following the fatal shooting of Mohsen Fakhrizadeh, who was considered Iran's top nuclear scientist, in November. Iran has blamed Israel for the shooting, according to the BBC and other news outlets.
The researchers found that on Dec. 2, the HMI web application was now asking for authentication to access the system, but the system was still accessible through the internet without any barrier, according to the Otorio report.
"Although this may prevent unskilled adversaries from accessing the system, those with a minimal toolbox can most likely compromise the system," the Otorio researchers note.
Also, the system still allows communications on port 502, which is used for Modbus protocol. "Modbus/TCP does not require any authentication/encryption. It is a bad practice to expose this interface directly to the worldwide web," according to the report.
The researchers note that one of the main reasons the reservoir was targeted is because the HMI system provided unprotected access. Moreover, the researchers suggest that the attackers did not possess any deep industrial capabilities or knowledge.
CISA Warning
Iranian attackers are reportedly becoming more proficient when it comes to their hacking operations. In an unrelated alert published Thursday, the U.S. Cybersecurity and Infrastructure Security Agency warned that Iran-based hackers are continuously improving their offensive cyber capabilities and targeting several U.S. federal agencies and other U.S.-based networks.
"They continue to engage in more conventional offensive cyber activities ranging from website defacement, distributed denial of service (DDoS) attacks, and theft of personally identifiable information (PII), to more advanced activities - including social media-driven influence operations, destructive malware, and, potentially, cyber-enabled kinetic attacks," the CISA alert notes.
CISA had also shared a similar alert in January describing the cyber threats associated with Iran following the U.S. assassination of General Qasem Soleimani, a prominent leader of the country’s military intelligence operations.
UAE Also Under Attack
In addition to the attack on the Israeli firm, Mohamed Hamad al-Kuwaiti, the head of cybersecurity for the United Arab Emirates, told an audience Sunday his country has also seen an increase in hacking following a historic deal that helped establish formal ties with Israel, according to Reuters.
While al-Kuwaiti did not provide details, he noted that financial institutions were targeted and that "traditionally many attacks in the region originate from Iran."