Card Not Present Fraud , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime
Feds Charge North Korean With Devastating Cyberattacks
WannaCry, Sony Pictures and Bangladesh Bank Attacks Tie to Suspect, FBI Says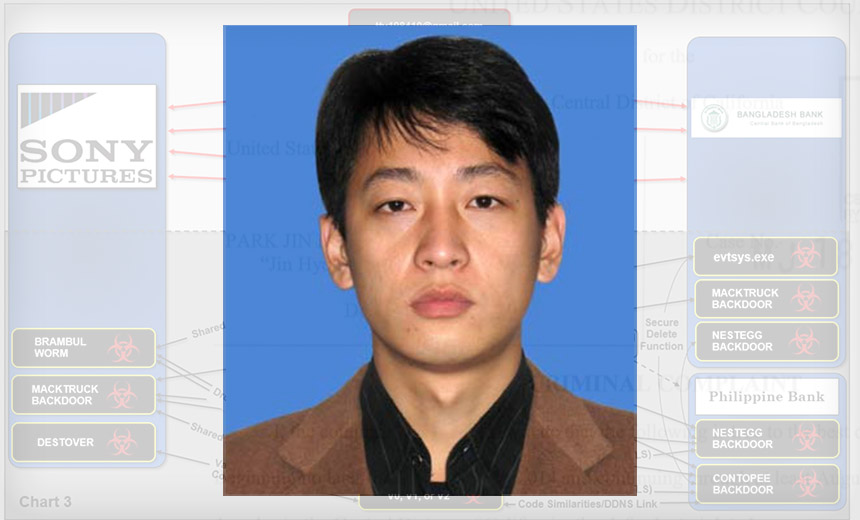
U.S. prosecutors have accused a 34-year-old North Korean man of involvement in some of the most destructive and profitable cyberattacks ever seen, including the WannaCry ransomware outbreak, the Sony Pictures Entertainment breach as well as the theft of $81 million from Bangladesh Bank.
See Also: Phishing Like the Bad Guys: Social Engineering's Biggest Success
On Thursday, the Department of Justice unsealed a criminal complaint against Park Jin Hyok, who is described as being proficient in multiple programming languages, network security and software development.

Park has been charged with conspiracy and conspiracy to commit wire fraud in federal court in Los Angeles. Although Park is believed to have lived in China between 2011 and 2013, he returned to North Korea in 2014 just prior to the attacks on Sony Pictures Entertainment.
Because the U.S. and North Korea do not have an extradition agreement, there's likely little chance that Park will be apprehended unless he travels to a country that cooperates with U.S. law enforcement.
The Justice Department says Park is not solely responsible for the attacks, and its investigation continues into others who may have participated.
The 179-page criminal complaint against Park contains a voluminous affidavit from FBI Special Agent Nathan P. Shields of the bureau's Los Angeles office. It contains extensive details that authorities say link both Park and the group he has worked with - often referred to as the Lazarus group - to a string of hacking devastation. Lazarus is also known as Group 123, Hidden Cobra and Nickel Academy.
"In sum, the scope and damage of the computer intrusions perpetrated and caused by the subjects of this investigation, including Park, is virtually unparalleled," the complaint says.
FBI: Park Reused Email Addresses
Park was a programmer who worked for the North Korean government, according to the complaint. He formally worked for a company called Chosun Expo in Dalian, China, which has been linked to Lab 110, a hacking division of the country's intelligence services, it says.
Park appears to have been identified, in part, because some of the Lazarus group's hacking activities became comingled with Chosun Expo email accounts. Park also frequently reused email addresses he established, as well as using the same infrastructure to access accounts that were later used for attacks, the complaint says.
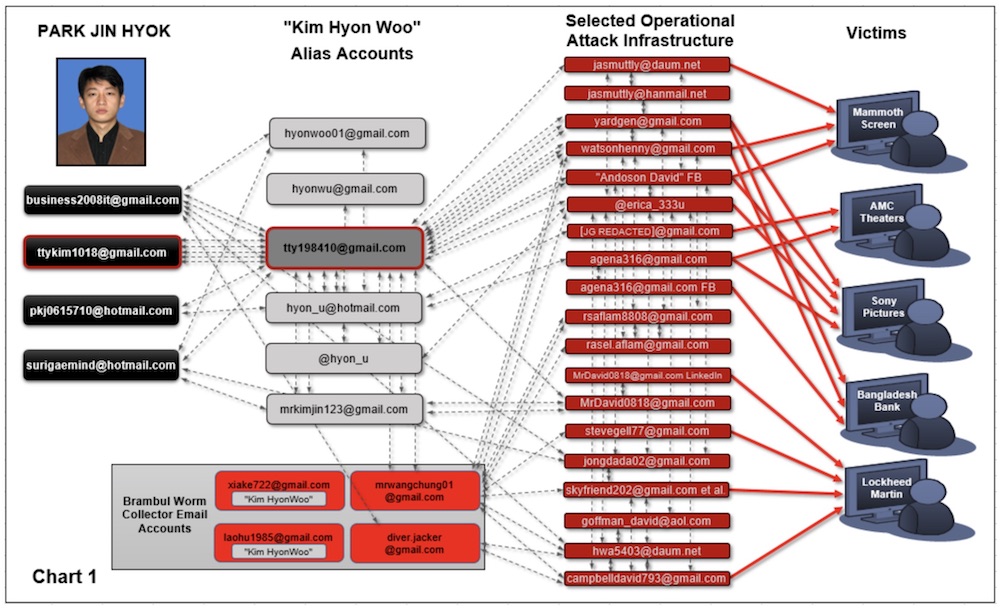
"Despite efforts to conceal his identity and the subjects' efforts to isolate the Chosun Expo Accounts from operational accounts that they used with aliases to carry on their hacking operations, there are numerous connections between these sets of accounts," the complaint says.
That sloppy operational security gave investigators plenty of threads to pull. Investigators filed 100 search warrants to gain access to 1,000 email and social media accounts with providers including Google, Facebook and Twitter, the complaint says.
Investigators say the North Koreans sometimes directly accessed accounts from North Korean IP addresses. Such attribution traits are often viewed warily because cyberattackers can purposely stage attacks in certain places in order to divert attention or direct blame. But for a well-resourced investigation - which likely involved signals intelligence that will not have been referenced in the criminal complaint - such clues often contribute to the bigger picture.
Strike Against Sony
Park has also been tied to the November 2014 attack against Sony Pictures Entertainment, which still stands as one of the most devastating attacks to have ever been executed against a company. In that case, a group calling itself the Guardians of Peace claimed responsibility for deploying malware that wrecked a computer's master boot record - a critical piece of code required whenever a computer starts to boot up, if it is to successfully start - which bricked the company's PCs (see Sony Pictures Cyberattack Timeline).
The group claimed the attack was punishment for the company's pending release of a film, "The Interview," that lampooned North Korean leader Kim Jong Un. Just a few weeks later, the U.S. blamed North Korea for the attack and later imposed new sanctions on the country.
At the time, some experts criticized the U.S.'s quick attribution, because authorities released no technical evidence to back up their assertions. Later, former FBI director James Comey let slip during a public talk that the Sony attackers failed to use proxy servers, which revealed North Korean IP addresses. The complaint against Park further reveals that the attackers sometimes directly accessed Sony's network from North Korean IP addressess (see FBI Defends Sony Hack Attribution).
In the months leading up to the Sony attack, the group peppered Sony employees and even actors with phishing emails and messages sent through bogus Facebook accounts that led to malware. One bogus Facebook account was used to send enticing messages claiming to have nude photos of A-list celebrities. The accompanying zip file contained malware, the complaint says. In the run up to the movie's release, the attackers also targeted employees of AMC Theatres with phishing emails that included malware-laden zip files, it adds.
Bangladesh Bank Heist
In February 2016, Bangladesh Bank lost $81 million after attackers created fraudulent SWIFT interbank messages and moved money out of the bank's account at the New York Federal Reserve. It remains one of the largest thefts ever from a bank and could have been even bigger; the attackers had attempted to steal $1 billion (see Bangladesh Bank Heist Probe Finds 'Negligent' Insiders).
The affidavit accuses Park and his group of using spear-phishing emails to gain access to Bangladesh Bank's systems. From there, the group created fraudulent money-moving requests within the bank's SWIFT system, exploiting the poor controls that the bank had in place.
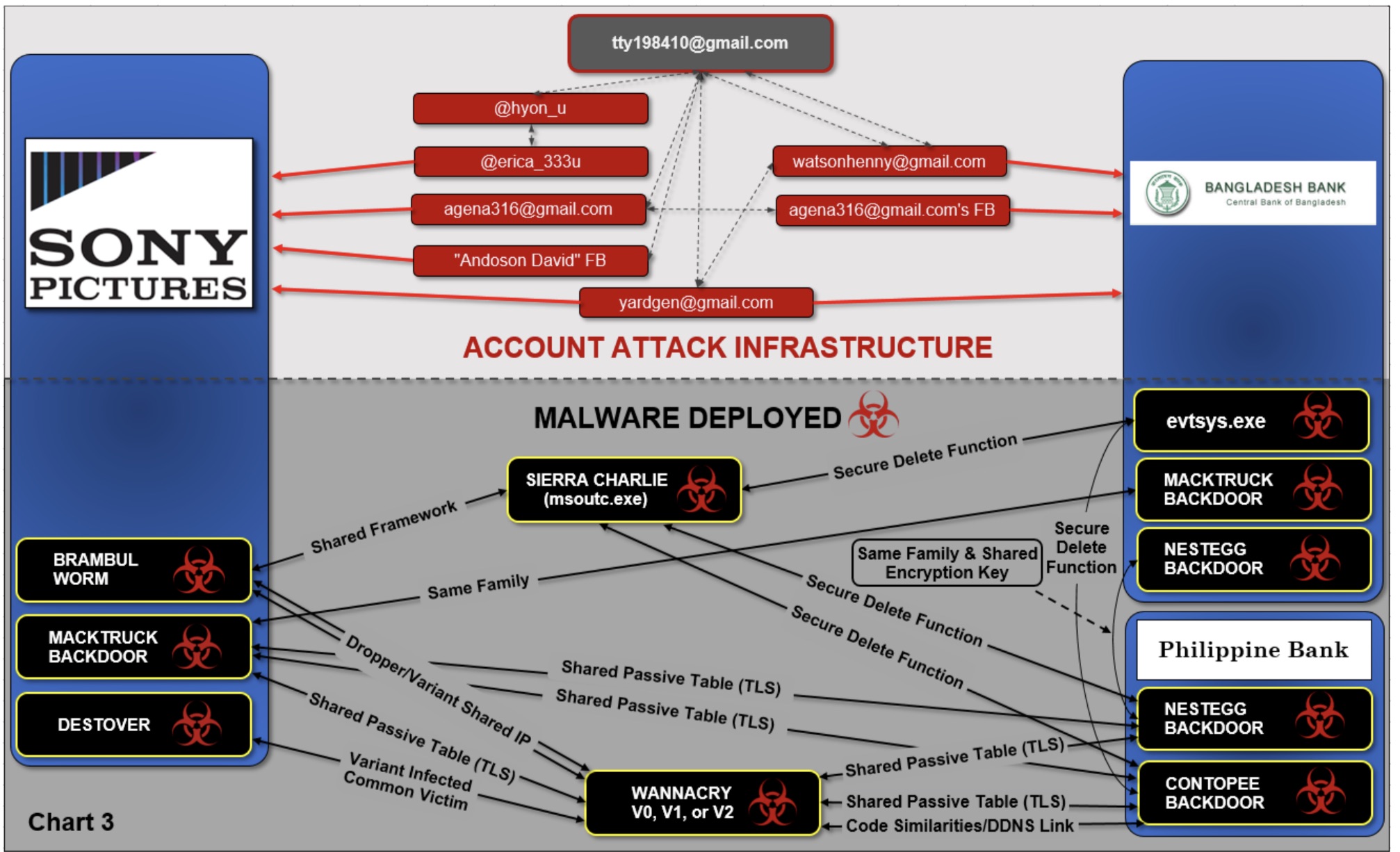
Investigators linked the Bangladesh Bank attack with the other attacks attributed to Park and Lazarus in part thanks to their use of a relatively scant number of email and social media accounts. "Some of the very same accounts were used to target Bangladesh Bank as were used to target some of the other victims discussed above, including SPE [Sony Pictures Entertainment]," according to the complaint.
For example, one email address, "watsonhenny@gmail.com," was used to sign up for a file-sharing service on Sony Pictures, the complaint says. That Gmail account's contact list also contained email addresses for Mammoth Screen, a British company that was targeted while it was producing a fictional show set in North Korea, as well as email addresses for 37 employees of Bangladesh Bank, it says.
Other victims that saw attacks from the same pool of accounts included banks in Vietnam and the Philippines, plus one bank in Southeast Asia, according to the complaint. Investigators say attackers also reused parts of the same malware in their attacks, as well as an inactive, static data table.
"The static data table was likely an inadvertent artifact that resulted when the subjects compiled multiple pieces of malware from source code to machine code when using that common library," the complaint says.
WannaCry Outbreak
The WannaCry ransomware, unleashed on May 12, 2017, still stands as one of the largest cyberattacks ever seen. The ransomware infected at least 300,000 systems worldwide, including 640 healthcare facilities in the U.K, plus transportation systems and multinational companies.
The version of WannaCry released in May was actually the third iteration of the ransomware, and the most potent version to date. That's because the malware included the ability to exploit a vulnerability in Microsoft's operating system, designated CVE-2017-0144, that appears to have been leaked or stolen from the National Security Agency. In addition, that version of WannaCry had been built to be a worm, allowing it to more easily spread.
Although Microsoft patched the vulnerability before details of the flaw were leaked, many organizations were not up-to-date with their Windows updates (see WannaCry Outbreak: Microsoft Issues Emergency XP Patch).
Investigators appear to have uncovered signs that the Lazarus group was actively looking to improve WannaCry after the first two versions and that they had actively investigated the leaked NSA vulnerability.
"Subjects using North Korean IP Address #6 were reading information regarding the development of code that would exploit the CVE-2017- 0144 vulnerability that was used in WannaCry Version 2," the complaint says.
The complaint, based on a technical analysis, alleges that Park and the Lazarus group are responsible for all three versions of WannaCry. The FBI's Cyber Behavioral Analysis Center concluded that the same author likely created all three versions based on language settings, metadata, timestamps and other details.
Also, investigators say they recovered the original WannaCry - referred to in the complaint as "Version 0" - from a computer of one victim. That version of WannaCry did not spread widely, as it wasn't engineered to be a worm. They also found that the same computer had been infected by malware called "Destover," which was the destructive malware that hit Sony Pictures, the complaint says.