Business Continuity Management / Disaster Recovery , Fraud Management & Cybercrime , Governance & Risk Management
Decryptor Bug Means Ryuk Victims Stuck in Ransomware Rut
Emsisoft Tool Can Fix Ineffective Attacker-Supplied Decryption - But Back Up the Files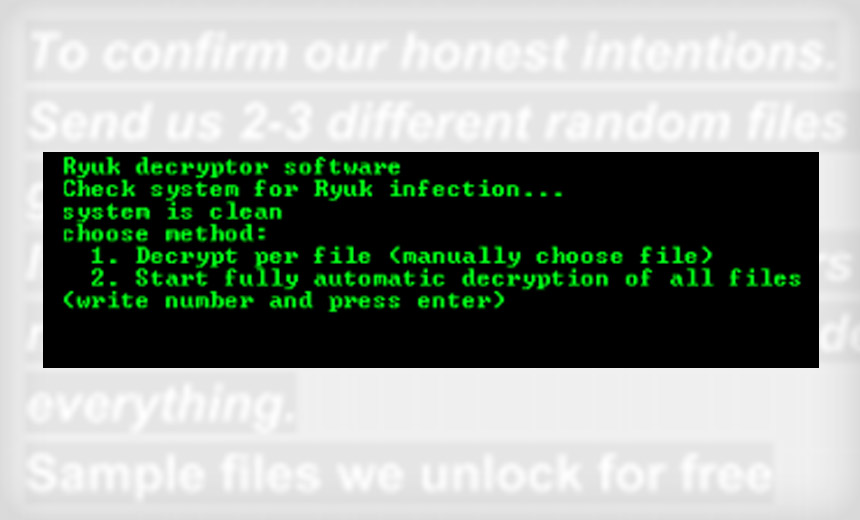
New Zealand-based security vendor Emsisoft has spotted an anomaly in one of the latest versions of the Ryuk ransomware - one of the most prevalent types of file-encrypting malware. A buggy decryptor supplied by the attackers wielding Ryuk may not work properly.
See Also: Mandiant Cyber Crisis Communication Planning and Response Services
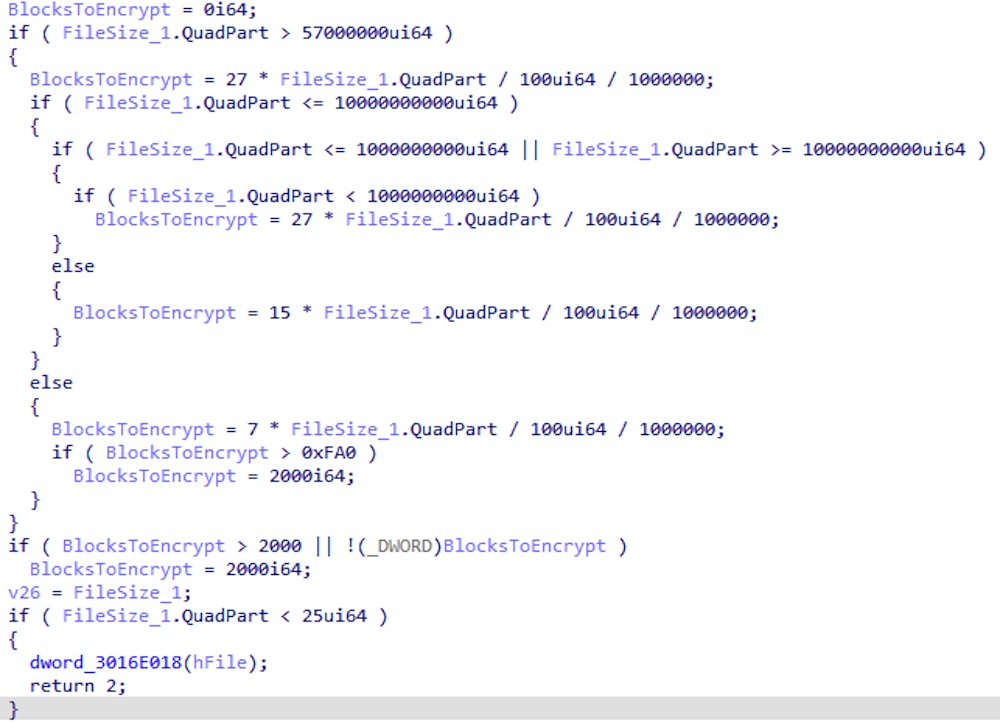
When encrypting files, Ryuk tries to save some time, but the effect on victims’ recovery efforts could be tragic.
Emsisoft’s Malware Lab writes in a blog post that this particular version of Ryuk handles files that are larger than 54.4 megabytes differently than smaller ones. In order to encrypt as many files as possible and as quickly as possible, it will only partially encrypt files larger than that size, the lab says.
Partially-encrypted files have a slightly different footer at the end of the file, Emsisoft wriites. The end of the file is where Ryuk – a descendant of the Hermes ransomware – stores a RSA-encrypted AES key that is used to encrypt the file, the company writes. There’s also a marker for how many 1MB blocks have been encrypted. Fully encrypted files don’t have the marker.
Truncated Files
Unfortunately, there’s a bug, which isn’t uncommon with ransomware.
The new changes to Ryuk means that the length of the footer is calculated differently, Emsisoft says. If the attacker-supplied decryptor tool is used, the files are truncated.
“Depending on the exact file type, this may or may not cause major issues,” Emsisoft says. “In the best case scenario, the byte that was cut off by the buggy decryptor was unused and just some slack space at the end created by aligning the file towards certain file size boundaries.”
The problem is dependent on the type of file that has been encrypted, such as Virtual Hard Disk files, which is a file format used by Microsoft that enables a disk-in-a-file abstraction.
Also, Emsisoft says Oracle database files “will store important information in that last byte, and files damaged this way will fail to load properly after they are decrypted.”
There’s also a big caveat: If someone runs this particular decryptor, it will erase the original encrypted files. That means if the encrypted files aren’t backed up and the files haven’t been properly decrypted, they’re gone.
Customized Decrypter
Emsisoft says it has developed a functional decryptor that will work on partially encrypted files.
Emsisoft is one of dozens of contributors to Europol’s No More Ransomware project, which aggregates the latest decryption tools developed by researchers. But the company's new decryptor is a paid tool due to the customization required to make it work for each individual infection, says Brett Callow, Emsisoft’s spokesman.
“This isn’t a tool that we can simply make available for download; each one requires work on our end,” Callow says.
So who’s affected? Callow says anyone who has been infected with Ryuk in the last two weeks could end up being supplied a faulty decryptor if they pay.
“If someone wants to use that [potentially faulty] tool, the best advice is to create a backup of the encrypted files before running it,” he says. “That way, they'll get a second bite at the cherry should things not work out well. In fact, the best advice is always to back up before using a decryptor, no matter where they got it.”
He estimates the maximum cost of Emsisoft’s custom tool would be about $500. Victims, however, will still have to pay the ransom. Emsisoft’s tool only replaces the defective decryptor supplied by the ransomware authors.
Ryuk: An Expensive Infection
Ryuk has proved to be a fearsome foe. It emerged around August 2018, and since then has tallied a steady stream of victims. In late November, global security company Prosegur reported some of its systems were down due to Ryuk infections (see: Security Firm Prosegur Hit By Ryuk Ransomware).
Ryuk also isn’t cheap to escape. Data published in February by McAfee and Coveware, which specializes in dealing with ransomware, found that the ransom amounts demanded by Ryuk are often 10 times more than average, “making it the costliest type of ransomware.”
“Coveware also observed that some Ryuk ransoms were highly negotiable, while others were not,” according to McAfee and Coveware. “The bar-belled negotiation results generated an average ransom payment of $71k, a 60 percent discount from an average opening ask of $145k.”
The biggest step an organization can take toward staving off ransomware or deal with its after-effects is to prepare in advance. Forrester published a comprehensive guide in June to paying off ransomware attackers if that’s the only option, and No More Ransomware has advice on how to prevent infections.