COVID-19 , Endpoint Security , Fraud Management & Cybercrime
Is COVID-19 Driving a Surge in Unsafe Remote Connectivity?
Remote Desktop Protocol: Experts See No Apocalypse, But Urge Better Defenses
The coronavirus has forced many more employees, including IT teams, to work from home. But questions persist over whether the surge in remote working is being done in a manner that prioritizes information security.
See Also: Cybersecurity for the SMB: Steps to Improve Defenses on a Smaller Scale
Many organizations, for example, already use remote desktop protocol to remotely access systems and servers. RDP enables IT departments to remotely and easily manage Windows systems. But poorly secured or unprotected RDP endpoints can provide easy access for hackers, too.
So it's concerning that on Sunday, John Matherly, the founder of internet of things device search engine Shodan, reported seeing over the past month a 41.5 percent spike in "the number of devices exposing RDP to the internet via RDP's default TCP port 3389." He also saw a 36.8 percent increase in RDP connections via the non-standard TCP port 3388, in an apparent "security by obscurity" move.
(Editor's note: Late on Tuesday, Matherly updated his blog post to remove specific percentage increases, saying "we're still seeing growth but significantly less than before" in internet-exposed RDP endpoints. Matherly says he revised the findings because his historical analysis looked only at IPv4 results, whereas the later analysis also included at IPv6 results.)
Matherly also reports that 8 percent of systems exposing RDP to the internet remained vulnerable to the serious BlueKeep flaw, which attackers can exploit to bypass authentication and gain direct access to a system.
No Long-Term Changes
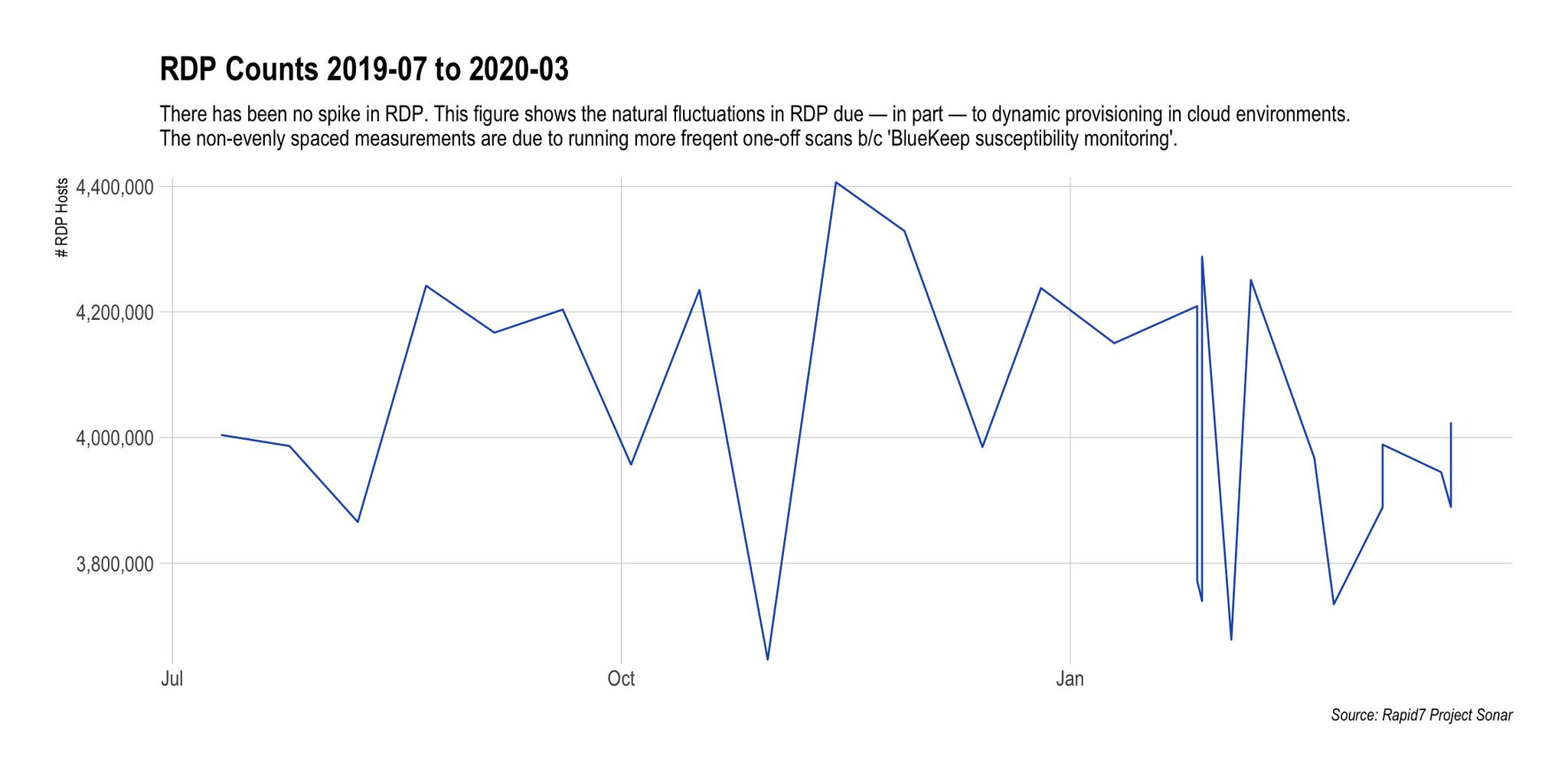
The good news is that other internet scanning services say they have seen no long-term changes in the prevalence of RDP. In other words, IT teams do not appear to have been in a mad rush to RDP-enable every endpoint.
Over the past six months, "the number of internet-exposed RDP devices has been stable, between 4.4 million to 4.7 million, in our data," Tiago Henriques, CEO of Zurich-based IoT search engine BinaryEdge, tells Information Security Media Group.
Another piece of good news, Henriques says, is that many of these devices are being exposed only with network-level authentication, as security experts recommend. NLA requires that anyone attempting to connect to a system via RDP first authenticate before they're allowed to establish a session.
Scans run by security firm Rapid7's in-house internet scanning project, Project Sonar, from July 2019 through this month have also seen no significant shift in overall levels of devices exposing RDP to the internet (see: Cyberattack Risk: Scans Find Big Businesses Exposed).
Inventory Everything
While internet-exposed RDP hasn't spiked, it also hasn't decreased. "The numbers are not apocalyptic, but if people were following advice to properly hide RDP, over time they should be down," says Stephen Cobb, an independent security and privacy researcher. In an earlier whitepaper on ransomware, he noted that as of Sept. 1, 2018, he counted 3 million internet-exposed RDP ports.
In short, too many organizations are continuing to use RDP in a manner that leaves their networks and thus data exposed to hackers (see: COVID-19 Complication: Ransomware Keeps Hitting Healthcare).
"Past experience predicts that a significant percentage of that access will be weakly protected at best, and we know that criminals have a wide range of tools at their disposal to take advantage of such access, whether for extortion, ransomware, data theft or sabotage," Cobb tells ISMG. "Sadly, the sense of being 'all in this together' in the fight against coronavirus is not felt by all criminals, and some will have no ethical qualms about abusing RDP for profit regardless of the impact on victims."
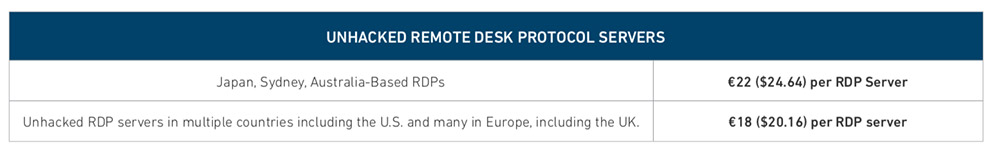
Indeed, stolen or brute-forced RDP credentials have been regularly sold for as little as $3 on darknet marketplaces. Many crime gangs continue to use RDP credentials to obtain remote access to a target network, conduct reconnaissance or steal all data of interest that can be resold on cybercrime markets or to nation-state actors. Then, they either resell the RDP credentials to less-skilled ransomware gangs, or they simply install crypto-locking malware themselves to further monetize the attack (see: Ransomware Gangs' Not-So-Secret Attack Vector: RDP Exploits).
BlueKeep Flaw Persists
Another threat to many organizations with remote services enabled is BlueKeep, a vulnerability that was first disclosed by Microsoft in May 2019, when it released a patch. The vulnerability, designated CVE-2019-0708, exists in many versions of Windows' remote desktop services - a widely used utility for connecting to remote computers. It allows an attacker to gain authentication-free access to a machine via RDP by using specially crafted requests.
The vulnerability exists in unpatched versions of Windows 2000, XP, Vista and 7, as well as Windows Server 2003, 2003 R2, 2008 and Server 2008 R2. (Windows 8 and later on desktops, and Windows Server 2012 and later on servers, do not have the flaw.)
In September 2019, researchers released proof-of-concept exploit code for the flaw. But two months later, 724,000 internet-exposed systems with the flaw remained unpatched as reports of mass exploits began rolling in (see: BlueKeep Attacks Arrive, Bearing Cryptomining Malware).
One risk that remains is attackers might find a way to craft a worm for targeting the exploit, which would enable a virus to spread directly from one vulnerable system to another.
Ideal: No Internet-Exposed RDP
Faced with the prevalence of poorly secured RDP, as well as endpoints still vulnerable to BlueKeep, organizations ideally should not be using any internet-exposed RDP. That's the thesis of a December 2019 blog post by Aryeh Goretsky, a researcher at security firm ESET.
Such an approach "may be problematic for some businesses, because there may be some seemingly legitimate reasons for this," Goretsky says. "However, with support for both Windows Server 2008 and Windows 7 ending in January 2020, having computers running these and being directly accessible using RDP via the internet represents a risk to your business that you should already be planning to mitigate."
To mitigate such risks, he recommends organizations first block RDP access via the internet, followed by testing for and patching BlueKeep as well as enabling NLA. Next, he recommends requiring long and strong passwords for all accounts that can be used to access RDP. In addition, he says two-factor authentication must be used to restrict access to any account allowed to access RDP, and he suggests that organizations require that any attempts to access RDP from outside the local network come in via a VPN gateway, so they can "enforce stronger identification and authentication requirements for remote access."
Bigger Picture: 6 Core Cybersecurity Controls
Focusing on using RDP in a secure manner is, of course, only part of the picture facing organizations that have had to shift to supporting massive remote workforces, seemingly overnight.
The shift is sure to attract extra attention from opportunistic gangs wielding ransomware or business email compromise schemes, says incident response expert David Stubley, who heads Edinburgh, Scotland-based security testing firm and consultancy 7 Elements.
"Given this, it is paramount that organizations take the time to ensure that they continue to maintain good cybersecurity hygiene while managing the wider risks associated to both employees and the wider business by COVID-19," Stubley tells ISMG.
"Keeping the show on the road" means ensuring organizations have tackled six core cybersecurity controls:
- Patch every system as quickly as possible to lower the organization's attack surface.
- Back up all data to enable the organization to quickly roll back or restore systems, especially after a ransomware attack.
- Take steps to secure remote access, for example, via VPNs, and lock down all remote touch points, such as via RDP.
- Ensure passwords are tough to crack and that new services get launched with strong passwords.
- Use multifactor authentication everywhere possible.
- Educate users about the latest phishing threats.
Bootstrapped Digital Transformation
As more organizations shift to a remote workforce, new working patterns and technology adoption - including shadow IT - may lead to corporate data suddenly being poorly secured or stored in a manner that violates regulatory requirements. And more systems may be spun up that fail to secure commonly used protocols, such as RDP.
"Changes to the network perimeter can also create unanticipated threats, as a higher burden is placed on remote-access systems, and if not correctly implemented, may expose systems to the internet," says Matt Linney, a senior security consultant at 7 Elements. "Looking at this now could save substantial loss in the future.”
The problem may be exacerbated by COVID-19 driving many organizations to rapidly embrace the equivalent of bootstrap approaches to digital transformation and moving to cloud-based platforms and core services without having first carefully planned, tested, validated and secured their approach (see: Zoom Fixes Flaw That Could Allow Strangers Into Meetings).
"Ensure that any new technology your organization deploys - such as cloud-based solutions - will enable you to deal with changes to working patterns and also meet backup requirements," Stubley says, noting that organizations must ensure they're tracking every technology roll-out - cloud or otherwise - across the organization.
He adds: "Another key question to ask would be: 'Do any of the changes we have implemented alter where our sensitive data is being held?'" That's significant, he says, because it has implications for disaster recovery as well as complying with regulatory requirements.
As always, having up-to-date and tested backups of corporate data - even when it's being stored in the cloud - is essential for recovering from attacks, regardless of how hackers get in. "Data backup remains critical," 7 Elements' Linney stresses. "In the event of a cyberattack, a regular data backup can minimize data loss and the potentially negative impact this can have on a business."