Business Email Compromise (BEC) , Cybercrime , Email Security & Protection
Business Email Compromise Targets Mental Health Provider
Experts Describe How to Avoid Falling Victim to These Scams
A recent attempt by hackers to trick a mental health provider into transferring funds serves as a reminder to other healthcare entities about the threat of business email compromises.
See Also: Spear Phishing: Top 3 Threats
In a July 29 breach notification statement, Seattle-based Community Psychiatric Clinic says it recently identified two data security incidents that potentially exposed patient and employee information.
One of those incidents involved an attempt “to induce CPC to engage in a fraudulent wire transfer of funds,” the healthcare provider reports.
BEC Attack
CPC says that on or about March 12, the organization became aware of a potential data security incident involving unauthorized access to one of its employees' Microsoft Office 365 email accounts.
”CPC immediately changed all passwords associated with the O365 account and restored the employee's hard drive, thereby terminating all potentially unauthorized access on March 12,” the statement says. “CPC also implemented additional security measures on this employee's O365 account to prevent any similar incidents from occurring in the future.”
In early May, however, CPC became aware of a separate potential data security incident involving unauthorized access to another employee's O365 account when a malicious actor attempted to induce CPC to engage in a fraudulent wire transfer of funds, the statement says.

“As a result of CPC's immediate efforts to investigate and remediate this event, all funds were recovered,” according to the statement,
CPC says that in response to that fraud attempt, it also immediately changed all passwords associated with the employee's O365 account, terminated all potentially unauthorized access on May 8, and implemented additional security measures on the account.
”As a result of these events and in an abundance of caution, CPC undertook a comprehensive external forensic investigation of its entire O365 environment to determine the nature of the data security incidents and confirm that all potential unauthorized access had been terminated,” the clinic says.
An external forensic investigation concluded that the O365 accounts involved in those two incidents, as well as two additional employees' O365 accounts, were potentially compromised. CPC says it immediately undertook efforts to cease any potential unauthorized access on the two additional identified accounts by changing passwords and implementing additional security measures.
The investigation did not identify any signs of data exfiltration or any access to CPC's servers or workspaces beyond the access to the four O365 accounts via Outlook Web Access.
“Ultimately, the data security incidents … may have resulted in unauthorized access to personal information and/or protected health information of current and former clients and employees of CPC,” the clinic acknowledges.
The company’s statement does not identify the type of PHI or employee information potentially compromised.
CPC did not immediately respond to an Information Security Media Group request for additional information about the incidents, including the amount of money involved in the fraud attempt, how the money was recovered and the number of individuals whose information potentially was exposed.
As of Tuesday, CPC data security incidents were not listed on the U.S. Department of Health and Human Services’ HIPAA Breach Reporting Tool website listing major health data breaches affecting 500 or more individuals.
Growing Threat
Businesses of all sizes and types are increasingly falling for business email compromise attacks, says attorney Christopher Ott of the law firm Davis Wright Tremaine, who is a former Department of Justice litigator.
“The number and value of BEC losses has increased every year since 2013,” he says. “Per FBI statistics, annual reported BEC losses are now in excess of $1.5 billion every year. The actual losses, which are not always reported, may be even higher.”
On Aug. 2, the Department of Justice announced a Nigerian national was sentenced to three years in prison for his part in business email compromise schemes “that targeted hundreds, if not thousands, of CFOs, controllers and others at businesses, nonprofit organizations, and schools in Connecticut and across the U.S.”
Steps to Take
Healthcare and other entities need to proactively defend against email fraudsters, says Caleb Barlow, who was recently named CEO and president of security consultancy CynergisTek upon the retirement of founder Mac McMillan.
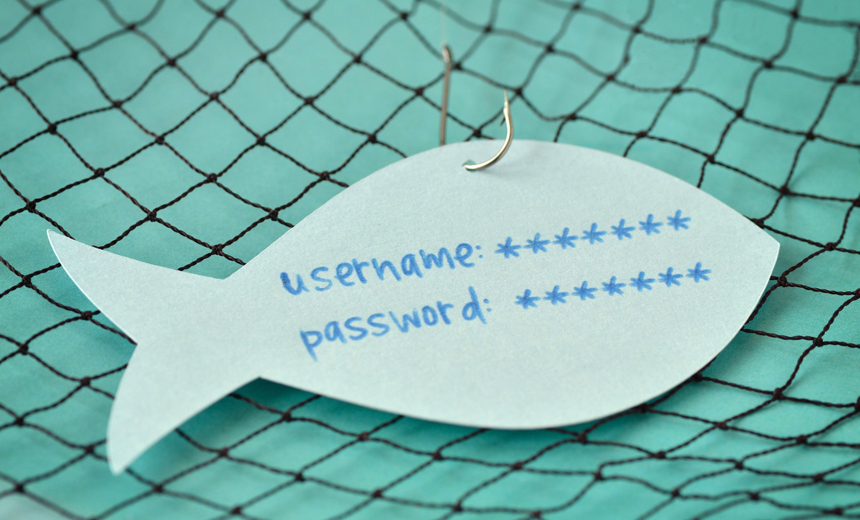
”E-mail compromises are a common challenge, particularly where companies are not using two-factor authentication. If your e-mail is only protected with a password and you are using that password on multiple sites, it is a pretty easy pivot for the adversary,” he says.
Security experts say it’s critical for entities to act quickly once a scam is identified or suspected.
”In this case speed matters,” Barlow says. “It is sometimes possible to reverse [fraudulent money transfers], but you need to notify the bank and law enforcement immediately. The better policy is to have the controls in place to prevent it from happening in the first place. As a policy, you should never be issuing orders to move money via just an e-mail message.”
Ott, the attorney, offers a similar perspective. “If you act within a day, most banks will help you to recover your money. If the delay is closer to a week, which is typical, the wires cannot easily be reversed,” he says.
”These BEC scams turn on two main factors: the casual manner with which we conduct business via email and exploiting that casualness into tricking victims into changing established payment procedures to include a new bank.”
To address these factors, all companies should raise red flags whenever a vendor requests a change in payment method, and all companies should incorporate procedures other than email into their payment processes, he adds.
”Healthcare entities, because of their size and the value of their services, provide tempting targets to BEC fraudsters,” Ott says. “However, these entities are actually better prepared than most business to combat these criminals because the discipline and rigor that HIPAA has forced upon them. If they strategically extrapolate and expand the same principles that they use in their PHI management to their vendor relationships, healthcare entities will find great success in preventing future events.”