Some Insider Threats Tough to Mitigate
Insiders Performing Mundane Tasks Often Make MistakesCan cybersecurity practitioners afford to be as merciful as Alexander Pope? The 18th century poet wrote, "To err is human; to forgive, divine."
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
Information technology is a very unforgiving environment. Incorrectly type one character and an application won't open. Absentmindedly click the reply all button, and an e-mail response intended just for one friend dissing the new outfit of another friend is also sent to the friend who is no fashionista. Oops!
Inattentiveness presents serious information security risks. A coding error by a programmer - simply, a high-tech typographical error - is believed to have caused the Heartbleed flaw (see The Marketing of Heartbleed).
Researchers who prepared the 2014 Verizon Data Breach Investigation Report issued earlier this month say they've come across more than 16,000 incidents in the past year where sensitive information was unintentionally exposed, such as an e-mail with an attachment containing proprietary information being sent to the wrong recipient. "Nearly every incident involves some element of human error," the Verizon researchers write in the report.
Alan Brill, senior managing director at Kroll Advisory Solution, acknowledges the frailties Pope wrote about three centuries ago. "Even with the best of intentions, people make mistakes," he says.
Toll of Boredom
The authors of the report put it more bluntly: "After scrutinizing 16K incidents, we've made a startling discovery - people screw up sometimes (Nobel Prize, here we come!). The data seems to suggest that highly repetitive and mundane business processes involving sensitive info are particularly error prone. It's also noteworthy that this pattern contains more incidents caused by business partners than any other."
That's a point Brill picks up on: "We used to think of it as being a regular employee, but ... there are now a lot of business partners, business associates, who provide services to us and are, relative to the outside world, insiders. There are temps; there are contractors; there are vendors; there's an entire ecosystem of organizations that collectively represent the insider. It's in that ecosystem that we see some of these problems."
The sectors Verizon identifies as the worst offenders of these miscellaneous errors are public, administrative and healthcare. Put the U.S. federal government at the top of that list. But that doesn't necessarily mean government workers are more lackadaisical than those employed in the private sector. As the Verizon report states:
"The United States federal government is the largest employer in that country, and maintains a massive volume of data on both its employees and constituents, so one can expect a high number of misdelivery incidents. Public data laws and mandatory reporting of security incidents also cover government agencies.
"Since we have more visibility into government mistakes, it creates the impression that government mistakes happen more frequently than everyone else's, which may not be the case. This is not unlike the way we see higher numbers of overall breaches in U.S. states that have had disclosure laws on the books the longest."
Misdelivery Woes
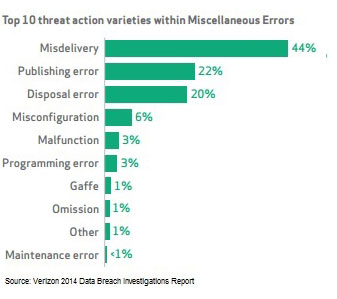
Misdelivery tops the list of insider threat actions within miscellaneous errors. The percentage for misdelivery would have been greater, but Verizon purposely excluded government data. "According to our sample," the Verizon researchers write, "government organizations frequently deliver non-public information to the wrong recipient; so much so, in fact, that we had to remove it from [the chart] so that you could see the other error varieties."
A common example Verizon researchers cite is a mass mailing where the documents and envelopes are out of sync and sensitive documents are sent to the wrong recipient. "A mundane blunder, yes, but one that very often exposes data to unauthorized parties," the report says.
Such unintentional conduct can be mitigated. "It's going to be important for organizations to recognize ... the unintentional, and try to determine if there are controls that can be effective both against the intentional insider in an organization as well as the unintentional insider," says Randy Trzeciak, senior member of the technical staff at the CERT Insider Threat Center within the Software Engineering Institute at Carnegie Mellon University.
How does your organization mitigate the risks posed by the unintentional insider threat? Share your thoughts in the box below.











