Cybercrime , Cybercrime as-a-service , Fraud Management & Cybercrime
Why Cybercrime Remains Impossible to Eradicate
Kelihos Bot Herder Offered Bargain Spam Campaign Pricing
More evidence that running cybercrime schemes remains inexpensive and accessible to anyone with criminal intent: To send spam emails, admitted botnet herder Peter Levashov quoted customers $500 for 1 million emails, $750 for 2 million emails, or $1,000 for 3 million emails, according to court documents (see Russian Pleads Guilty to Operating Kelihos Botnet).
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
And that was just his 2016 pricing. By 2017, Levashov was quoting customers rates that began at $300 for 1 million spam emails, payable in bitcoin, according to court documents. But he allegedly charged more if those emails were to be used in phishing, ransomware or other more complicated types of campaigns.
At the time of his arrest in 2017, Levashov's Kelihos botnet had 50,000 malware-infected and thus compromised - aka zombie - endpoints, prosecutors say.
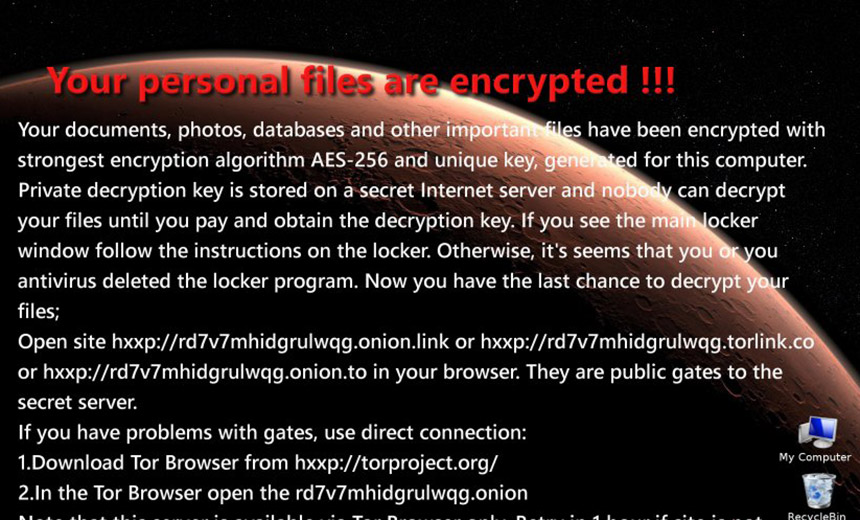
On Wednesday, Levashov - aka Peter Severa - pleaded guilty to a number of charges, including running and advertising spam and malware distribution services that attempted to infect PCs not only with banking Trojans but also such crypto-locking ransomware as JokeFromMars - reportedly a poor knockoff of CTB-Locker. Kelihos zombies could also be used to launch distributed denial-of-service attacks.
Malware used by Levashov could turn PCs into spam distribution cannons, while also raiding victims' PCs for contact lists that he used to distribute spam, according to court documents. He also admitted to using victims' email addresses to help distribute spam.
Burgeoning Cybercrime Economy
Levashov, however, was but one player in the massive cybercrime-as-a-service economy (see Cybercrime as a Service: Tools + Knowledge = Profit).
This economy continues to provide would-be criminals with easy access to an array of purpose-built and on-demand tools and services, including hosted infrastructure, as well as cryptocurrency, which enables them to somewhat anonymously pay for tools and services, and in the case of ransomware, extortion and other shakedown rackets, receive payments from victims that may be tough for authorities to trace.
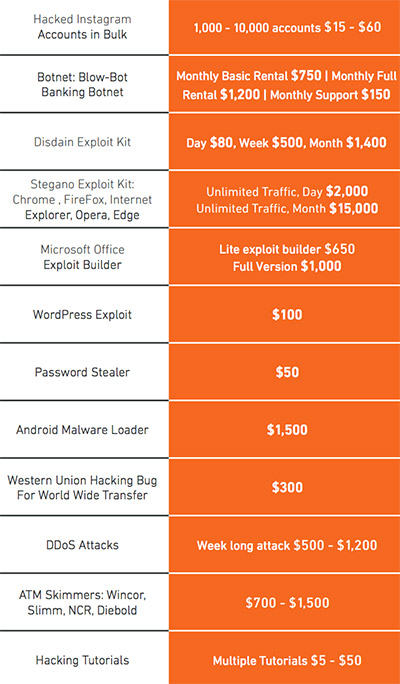
Cybercrime forums - some on "darknet" sites reachable only using the anonymizing Tor browser - offer for sale hacked bank accounts, customizable bank Trojans, remote desktop protocol access credentials to businesses, exploit kits, money mule services and payment card data and "fullz" (see How Much Is That RDP Credential in the Window?).
Cybercrime continues to be cheap and easy, especially when compared to its real-world analogs.
"Effectively, criminals are simply swapping conventional crime for cybercrime," University of Surrey computer science professor Alan Woodward told me back in 2016. "Why walk into a bank with a sawed-off shotgun when you can phish for money?"
These dynamics haven't changed; the tools at criminals' fingertips have become easier to procure and use (see Cybercrime: Ransomware, CEO Fraud Still Going Strong).
Levashov, for example, admitted to using bulletproof hosting services as part of his attacks. Such services charge a premium for hosting while promising to look the other way, for example, when said services might be used to store exfiltrated personally identifiable information or payment card details from malware victims.
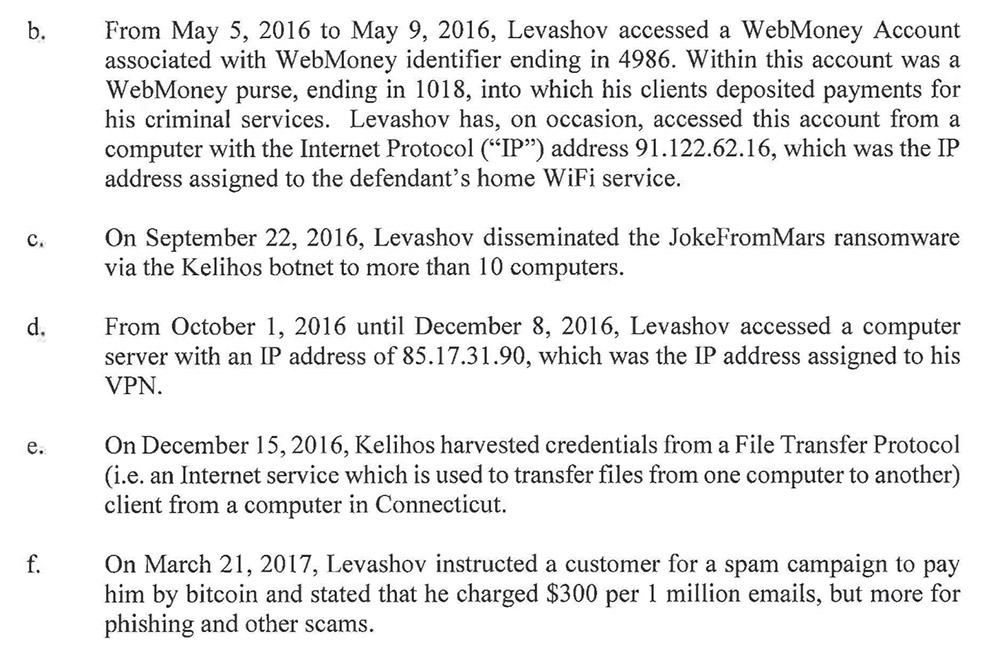
Prosecutors say Levashov also used virtual private networks to try and disguise his identities and activities. Many security experts recommend using VPNs, especially when connecting to public WiFi. But like many such services, they can also provide a degree of anonymity for criminals - provided authorities aren't able to subpoena customer records from a service provider.
Teen Cybercrime Power
Part of the problem with stopping cybercrime is that it tends to be transnational. In addition, law enforcement experts say many cybercrime gangs continue to operate from within Russia or its former Soviet satellites, including Ukraine, with which extradition treaties are complicated or nonexistent (see Cybercrime Groups and Nation-State Attackers Blur Together).
"Why walk into a bank with a sawed-off shotgun when you can phish for money?"
—Alan Woodward
Despite ongoing arrests of cybercrime service providers, new entrants continue to hit the market. Many of the budget services being offered today have been cooked up by teenagers or twentysomethings operating from various parts of the world (see Teen Hacker Avoids Jail Over On-Demand DDoS Attacks).
That includes two teenagers from Israel - with help from another teen in England - in the case of stresser/booter service vDos, which authorities shuttered in 2016. Moscow-based security firm Kaspersky Lab says that between April and July 2016, "vDos launched more than 277 million seconds of attack time, or approximately 8.81 years' worth of attack traffic."

The same year, British police arrested another teenager, who pleaded guilty to running Titanium Stresser, which police say was tapped by customers to launch 1.8 million attacks over a two-year period (see DDoS Stresser/Booter Services Feel the Heat).
Such services are typically inexpensive to procure, with DDoS attacks often costing $10 per hour or $200 per day, according to a review of cybercrime forums services published by cybersecurity firm Armor in March 2018.
Russian Cybercrime Rules
Engaging in cybercrime leaves thieves at risk of arrest. But for gangs based in Russia, experts say there's long been a tacit understanding that so long as criminals do not make victims of anyone inside the country, authorities will turn a blind eye, although they may occasionally request hackers to do them a patriotic online attack favor (see Russian Cybercrime Rule No. 1: Don't Hack Russians).
In the case of Levashov, after two decades of cybercrime, the St. Petersburg resident chose to go on vacation with his wife and son in Barcelona, where he was arrested by Spanish police at the request of the FBI.
His arrest followed busts of other Russian nationals - all alleged cybercriminals wanted by the FBI - as they traveled abroad, including in the Maldives, Prague and Amsterdam (see Hackers' Vacation Plans in Disarray After Prague Arrest).
While the U.S. Justice Department would then file an extradition request with authorities, so too, typically, would Moscow, often on some minor charge. To date, however, none of these Russian requests have succeeded in seeing one of its citizens get returned in lieu of doing time elsewhere (see Russia's Accused Hacker Repeat Play: Extradition Tug of War).
Justice, then, does get served, at least for some cybercriminals. But at least so far, it hasn't been enough to deter others from choosing a life of cybercrime.











