3rd Party Risk Management , Endpoint Security , Governance & Risk Management
Analysis: How Biden Executive Order Mirrors FDA's Cyber Plans
Do Their 'Software Bill of Materials' Proposals Face Uphill Battle?
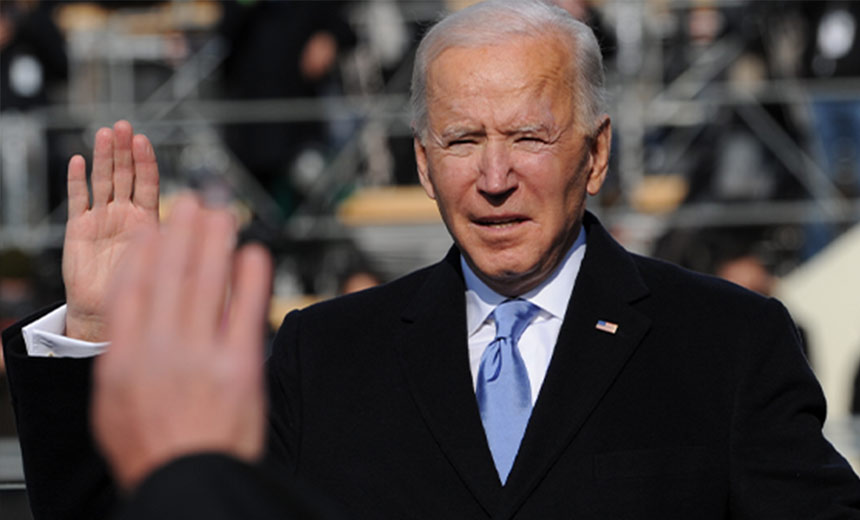
President Biden's recent executive order for bolstering cybersecurity of the federal government contains provisions for enhancing supply chain security that are similar to some of the efforts already under way by the Food and Drug Administration to improve the cybersecurity of medical devices.
See Also: What GDPR Means for Cybersecurity
But some of the ideas being touted by the government - such as a software bill of materials - could face an uphill battle, some experts note.
"While the executive order was nice, it is already too late," says former healthcare CIO David Finn, an executive vice president of the security consultancy CynergisTek.
"If organizations were not already doing these things, it is simply because they have chosen not to - for reasons both good and bad, I am sure. Given that so few were doing them, it may be time do more than ask."
Similar Efforts Involving Healthcare
In comments recently submitted in response to the National Institute of Standards and Technology's call for government agency feedback on Biden's executive order, the FDA urges NIST and the National Telecommunications and Information Administration "to continue with and enhance their present approaches to the development of standards and guidelines for Operational Technology security by leveraging experts from across the public and private sectors."
Practices and efforts presently underway at the FDA for OT cybersecurity encompass "the greater medical device security ecosystem," the FDA writes.
Specifically, the FDA notes that several of its existing documents - including draft and final guidance material - mirror various proposals contained in the Biden executive order, which was issued May 12 (see: Biden's Cybersecurity Executive Order: 4 Key Takeaways).
For instance, the FDA's draft updated cybersecurity guidance for the premarket of medical devices, issued in 2018, contains a proposal for a "cybersecurity bill of materials" that would list components susceptible to vulnerabilities. An updated version of that guidance is expected to be released by the FDA later this year.
Similarly, provisions in Biden's executive order call for the Department of Commerce, in coordination with the NTIA, to publish "minimum elements for a software bill of materials, or SBOM," for software products purchased and used by the federal government.
"The security and integrity of 'critical software' - software that performs functions critical to trust - is a particular concern," the executive order notes.
"Accordingly, the federal government must take action to rapidly improve the security and integrity of the software supply chain, with a priority on addressing critical software."
Statutory Authority
But while the FDA has proposed that medical device makers take actions to improve the cybersecurity of their products, such as providing a cybersecurity bill of materials for them, those provisions have been contained in nonbinding voluntary guidance and draft guidance, rather than in regulatory mandates.
In its comments to NIST, however, the FDA notes that its Medical Device Safety Action Plan of 2018 - as well as the Department of Health and Human Services ' fiscal year 2020 and fiscal year 2021 congressional budget justifications documents - also outlined plans "to consider potential new premarket statutory authorities" to require firms to take steps on medical device security.
“Currently, there is no statutory requirement - pre- or post-market - that expressly compels medical device manufacturers to address cybersecurity," the FDA writes.
Specifically, the FDA says it seeks to "require" that:
- Medical devices have the capability to be updated and patched in a timely manner;
- Premarket submissions to the FDA include evidence demonstrate the capability, from a design and architecture perspective, for device updating and patching;
- A phased-in approach to a medical device cybersecurity bill of materials is taken, including a list of commercial, open-source and off-the-shelf software and hardware components that are or could become susceptible to vulnerabilities;
- Device firms publicly disclose when they learn of a cybersecurity vulnerability so users know when a device they use may be vulnerable and provide direction to customers to reduce their risk.
"The proposal also seeks to improve proactive responses to cybersecurity vulnerabilities," the FDA writes.
New Mandates?
So, should Congress consider legislative moves to potentially expand the FDA's statutory authority to mandate - rather than just recommend - that medical device makers take specific actions to improve the cybersecurity of their products, pre- and post-market?
Mitch Parker, executive director of information services at Indiana University Health, suggests that, instead, "the best first step" is using the executive order's requirements to better incorporate cybersecurity into the Federal Acquisition Regulation.
"The federal government is one of the largest purchasers of medical devices in the world, considering the needs of the Veterans’ Administration, Defense Health Agency, Defense Logistics Agency, the uniformed services’ logistics commands, and smaller agencies such as the Indian Health Service," Parker notes.
"Establishing a good set of standards across agencies as part of FAR that are based on well-established industry standards and best practices, including ISO/IEC 11703, UL 2900-1, ISO/TC 215, and NIST’s own guidance, which also links very well to ISO, will provide the manufacturers a road map of where to go."
Turning Up the Heat
But Finn says now could be the time to turn up the regulatory heat on device makers.
"It has become abundantly clear that while progress has been made under current processes and structures, it is woefully inadequate in relationship to what the threats are and how they are progressing," he says.
"It is time to require medical device makers to 'build security in' when they design and build products," he says. "It is unfortunate that business is not compelled to do things the 'right' way, just as standard business practice."
For instance, medical device makers providing an SBOM for their products could greatly help healthcare customers, such as hospitals and clinics, be better informed and more proactive about the potential components in those devices that pose security risk.
"One of the major issues with security has been the inclusion of third-party components that raise security concerns," Parker says. "Knowing what is in the devices helps provide a more detailed picture of the risks so that organizations can take action to mitigate them before they can become a major issue."
Previous Proposals
But the software bill of materials "is not a new idea," Finn notes.
"It was clearly laid out in the Health Care Industry Cybersecurity Task Force report, which was sent to Congress at their request four years ago this month," he says, referring to a cybersecurity advisory group for HHS created by the Cybersecurity Information Sharing Act of 2015.
The task group, of which Finn was a member, issued a comprehensive report to Congress in June 2017, containing dozens of recommendations for improving healthcare sector cybersecurity (see: Analysis: Are HHS Cybersecurity Recommendations Achievable?).
But government and much of the healthcare sector "failed to act on it," he says.
"Transparency and shared cyber information are the enemies of bad security. The software bill of materials is important so that organizations, and even concerned consumers, can manage these assets, because first you must understand what is on those systems to determine if the technologies are impacted by known threats or vulnerabilities."















